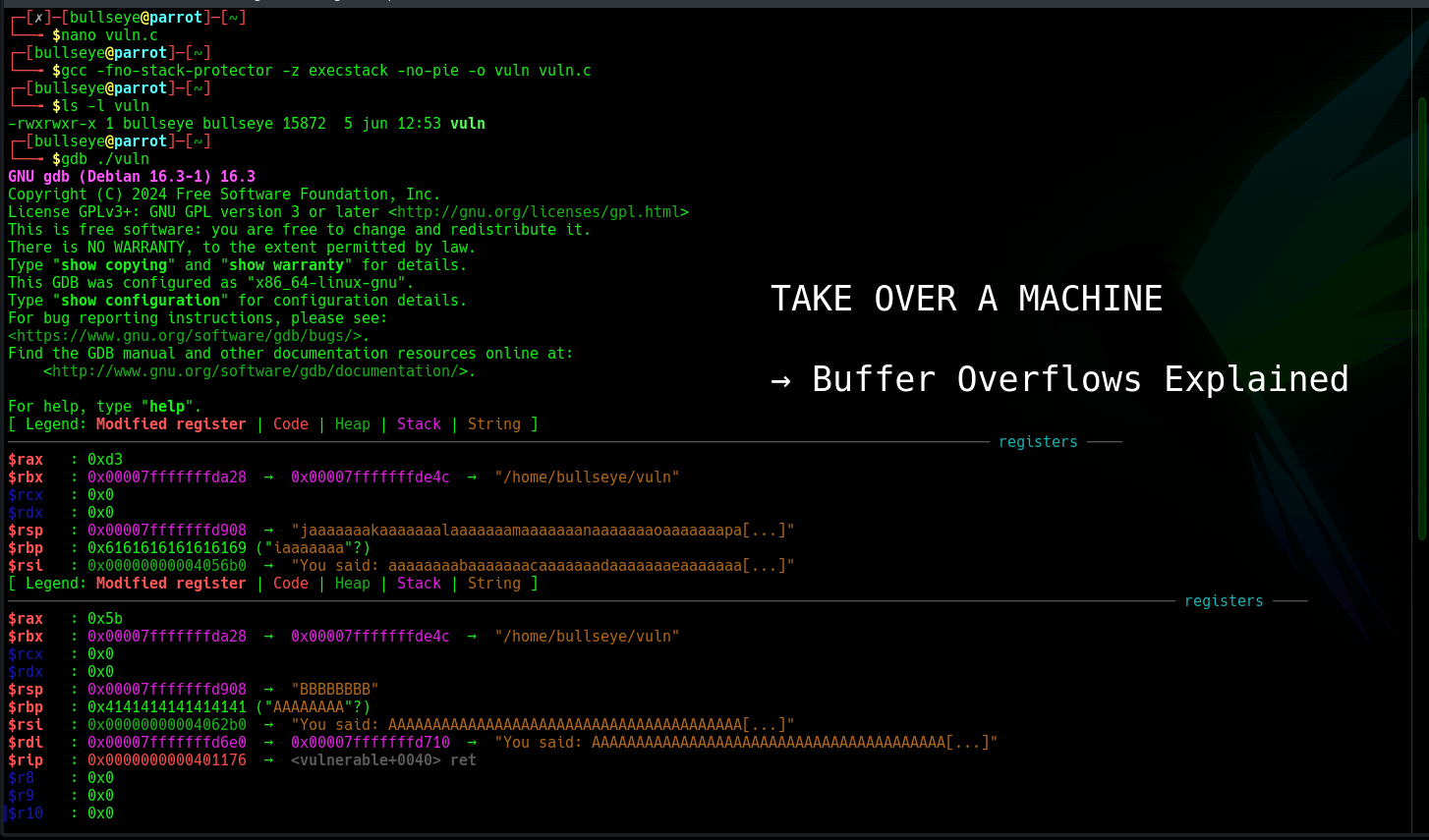
Watch a Buffer Overflow Take Over a Machine on Your Own Lab
Buffer Overflows: The Oldest Way to Take Over a Machine, and How to See It Work on Your Own Lab
Give a running program more data than it was built to hold, and on a lot of systems that extra data does not just get thrown away. It spills into the memory right next to it. And with a little care, that spilled data ends up running as code, with full control over the machine.