Microsoft Bing CVSS 10.0: CVE-2026-33819 Remote Code Execution Explained
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
Hacking is not a hobby but a way of life!
Bing had a CVSS 10.0 vulnerability in its backend infrastructure, the same infrastructure that powers Edge, Windows Search, and Copilot integrations across Microsoft’s ecosystem. Microsoft fixed it on March 10 without saying a word publicly. The CVE showed up six weeks later, on April 23. Nobody outside the company knew this had been sitting in the infrastructure that hundreds of millions of people use every day.
The CVE number is 2026-33819. The vulnerability class is deserialization of untrusted data, and the idea behind it is simpler than it sounds.
Deserialization of untrusted data means an attacker can inject code that executes the moment the application processes incoming data it was already expecting to receive. Microsoft has not disclosed which specific part of Bing’s infrastructure was affected or what the exact attack path looks like, but the CVE confirms anyone on the network could reach it without an account or anything required from the person on the other end.
The full CVSS vector is:
| |
The changed scope part is what pushes this to a perfect 10: the damage can extend beyond the original service boundary, reaching systems connected to it.
If someone successfully exploits this, they are running code on the servers handling Bing’s backend. Potential impacts include unauthorized access to data handled by those servers, lateral movement within Microsoft’s cloud environment, and manipulation of what comes back out: search results, AI responses, anything the backend produces. None of that is guaranteed, because it depends on how the affected component sits within Microsoft’s internal architecture, but the CVSS score reflects that the risk extends beyond the vulnerable component itself.
Microsoft rates this one as “Exploitation More Likely,” and that is not a label they put on every CVE. It means their own team looked at this and concluded that writing a working exploit for it was realistic, not a long shot. At the time of writing there is no confirmed exploitation in the wild and no public proof of concept. But in security, not knowing that something happened is not the same as knowing it did not.
Six weeks passed between Microsoft patching this internally and anyone outside the company knowing it existed. Microsoft labels this type of vulnerability “exclusively-hosted-service,” which basically means the fix is theirs to push, not yours to install. Microsoft pushed a build to their infrastructure and the exposure ended on their end. They also published zero workarounds or alternative mitigations for this one, which means even if the vulnerability had been public knowledge from day one, there was nothing anyone on the outside could have done to reduce the exposure. That is both how it should work for a cloud service, and also exactly the problem: nobody outside Microsoft could see any of it happening. During the period this existed, anyone using Bing-backed services was simply in the dark, with no way to tell whether the infrastructure processing their searches was being used against them.
CVE-2026-33819 was not the only vulnerability sitting in Microsoft’s search and AI infrastructure around the same period. CVE-2026-32186 is a server-side request forgery issue in Bing that could be used to escalate privileges. CVE-2026-33102 is an elevation of privilege vulnerability directly inside Microsoft 365 Copilot, scoring 9.3. The attack method is an open redirect: Copilot can be made to send a user to an untrusted site, and that redirect is how the privilege escalation happens. Most coverage of this CVE skips that detail entirely. Multiple vulnerabilities in the same stack, all patched quietly without much noise.
Here is what to check and do:
- → Copilot, Edge, Windows Search, and Microsoft 365 are running against patched infrastructure. Nothing to install or update on your end for this one.
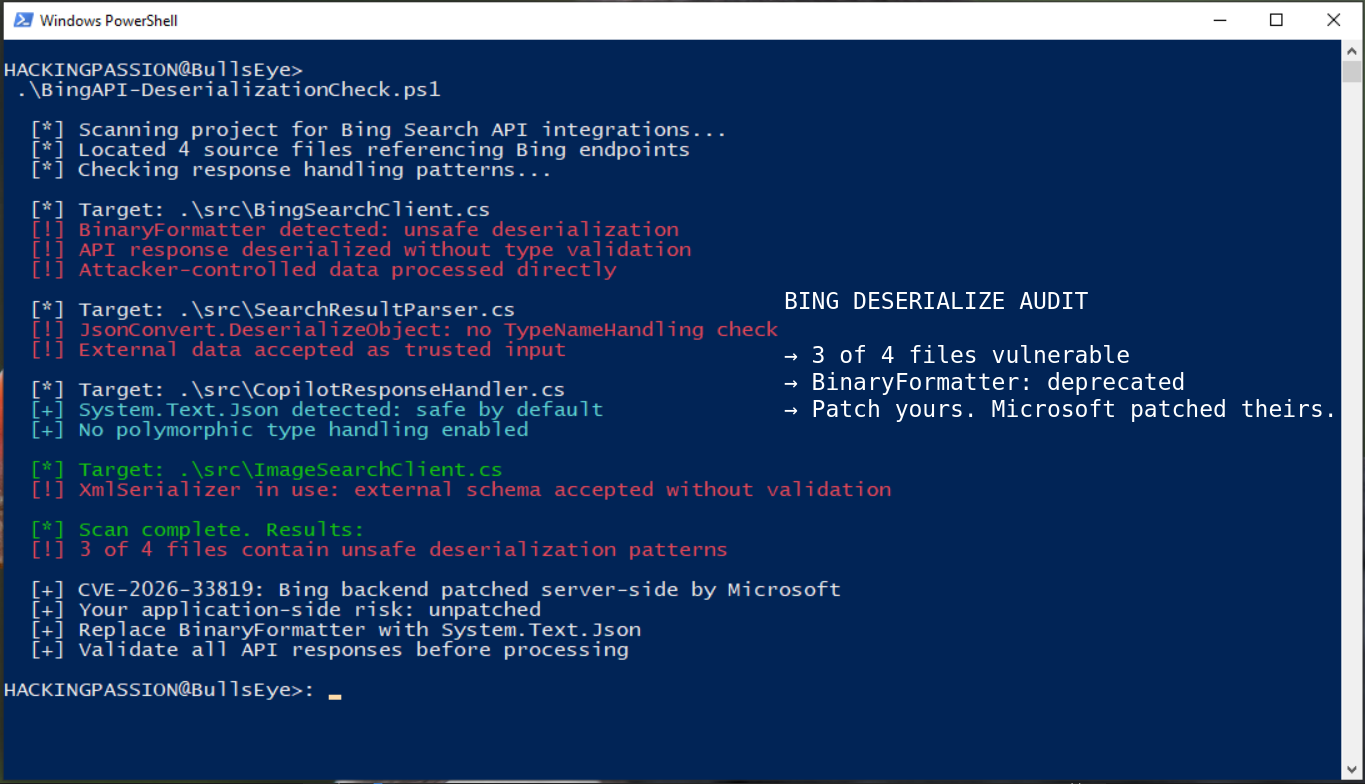
- → If your own code calls the Bing Search API and processes the response without validating what comes back, that is worth a separate look. The Bing-side issue is patched, but how your own application handles data coming from external APIs is always a separate question.
- → Check Microsoft’s Security Update Guide for cloud-hosted CVEs. Microsoft now publishes them regularly, and the fix is usually already deployed by the time anyone sees the disclosure. Knowing what just got quietly patched is how you understand how long any exposure window actually was.
- → If any part of a workflow runs through Microsoft cloud services, Patch Tuesday cloud advisories are relevant reading. This is not just something for enterprise security teams.
Web application exploitation, CVE research and real exploit hunting, post-exploitation, and privilege escalation on both Windows and Linux are all part of my ethical hacking course.
Hacking is not a hobby but a way of life.
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.