DesckVB RAT Uses Windows' Own Tools to Stay Hidden and Leaves Almost Nothing Behind
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
(The link supports me directly as your instructor!)
Hacking is not a hobby but a way of life!
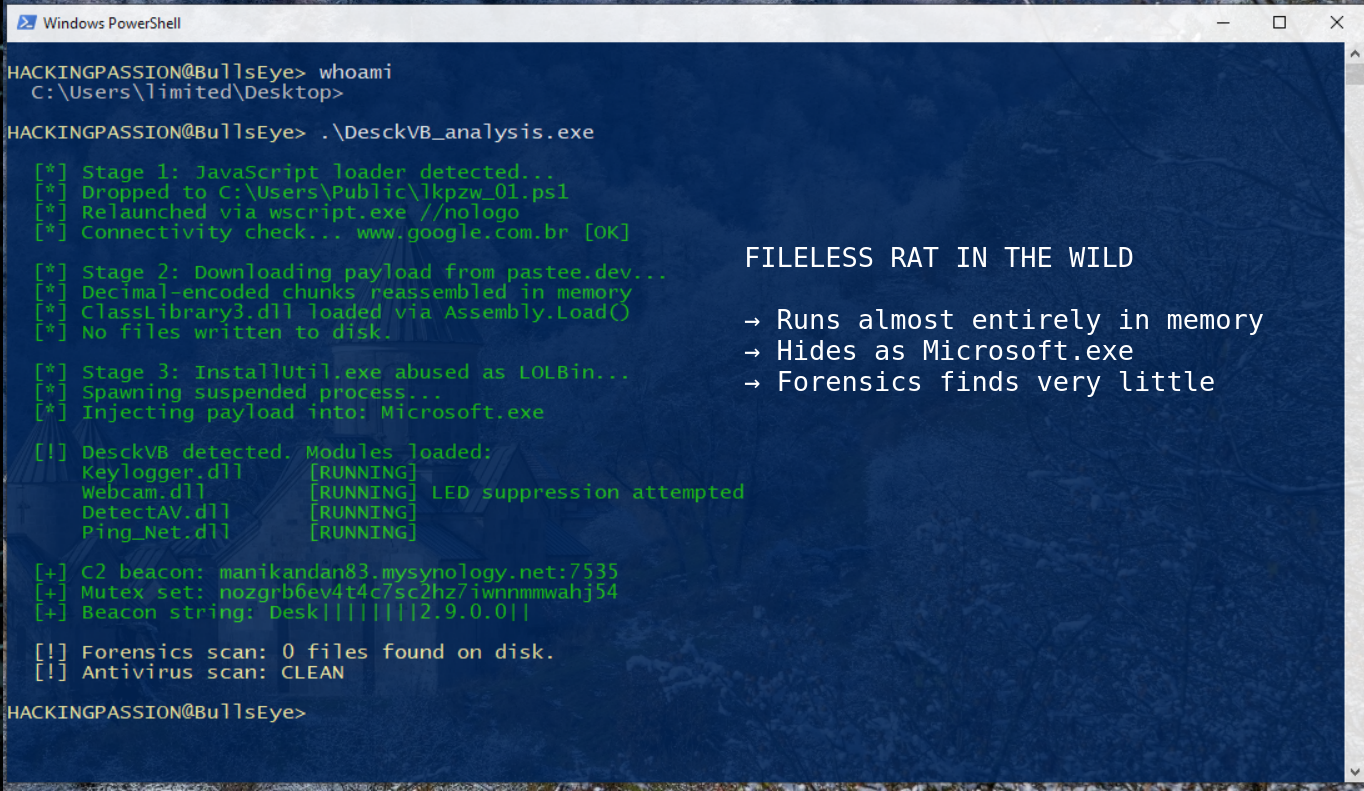
A Remote Access Trojan called DesckVB has been actively hitting systems throughout 2026, running almost entirely inside memory with barely anything written to disk, hiding its final payload inside a process it names Microsoft.exe, and attempting to switch off the camera LED before streaming video back to the attacker. A cracked version of the builder is already circulating freely, meaning attackers with minimal skills can deploy this today without writing a single line of code. Forensics teams sweep these machines afterward and find very little. The system looks completely clean. 😏
The infection starts with a JavaScript file. Nothing unusual about that on the surface. But the moment that file runs, it quietly copies itself into C:\Users\Public and relaunches itself through wscript.exe with a //nologo flag, which hides the window so nothing appears on screen. It also builds its own next step on the fly using Base64 encoding with the strings written backwards, which is a trick to fool security tools that look for known attack patterns in code.
The PowerShell script that follows does something telling before it does anything else. It pings Google to confirm there is an internet connection before doing anything further. If the check fails, the malware stops right there.
Once the connectivity check passes, the script reaches out to a server and downloads the next piece of the attack in small chunks, encoded as numbers. Those chunks are put back together inside memory into a file called ClassLibrary3.dll, which is then loaded and run directly from memory using Assembly.Load(). The payload hosting domain is pastee.dev, a legitimate paste site that most corporate firewalls never block. That is a deliberate choice: by hosting payloads on trusted infrastructure, the outbound connection looks like normal traffic. No file ever touches the disk after that first stage. This is what fileless execution looks like in practice: the malicious code exists only inside the running process, which means a traditional antivirus scan finds almost nothing to flag.
The loader uses InstallUtil.exe to run its code. InstallUtil.exe is a legitimate Windows tool that comes with the .NET Framework and is normally used by developers to install software components. This technique is called living-off-the-land, which means the attacker uses tools that Windows already comes with so the activity looks like normal system behavior. The final payload, named Microsoft.exe, is injected into a process that is started but immediately paused, before it ever gets a chance to do anything. This is a way to run code inside a process that already looks legitimate.
Before any of the malicious activity starts, the malware checks whether it is being watched. It actively scans for debuggers and analysis tools. If it detects one, it simply stops. This is why automated security tools that analyze suspicious software in a controlled environment so often miss it entirely. The malware recognizes it is being analyzed and does nothing.
At this point the attacker has a fully functional remote access trojan running in memory with no disk artifacts, hidden inside a process named after Microsoft itself.
Here is what DesckVB RAT can do once it is running.
The keylogger tracks every keystroke, records which window was active at the time, and intercepts clipboard content. The webcam module streams live images back to the attacker using DirectShow and specifically the AForge library, which is an open-source .NET framework for image processing. The attacker did not build this from scratch but plugged in a known library. And here is the detail that stood out in the research: the webcam module specifically tries to turn off the camera LED by changing a setting in the Windows registry before it starts recording. It does not always work, because whether the LED can be controlled depends entirely on the laptop or webcam manufacturer, but the intent is clear. Someone put effort into making sure the light does not turn on.
There is also a module that checks which antivirus software is installed on the machine and sends that list back to the attacker before doing anything else. The attacker knows exactly what security tools are present before making another move.
There is a fourth module called Ping_Net.dll that is rarely mentioned in any coverage of this malware. It does more than just test connectivity. On the mapa command from the attacker, it fetches any URL the operator sends it, using the infected machine as a browser pointed wherever the attacker wants. It also uses www.google.com.br specifically for its connectivity check, which is another indicator pointing toward a Brazilian origin.
The communication channel uses encrypted HTTPS traffic over port 443, which is the same port as ordinary web browsing. Everything looks like normal internet traffic from the outside.
Now about attribution. In cybersecurity, attribution is one of the hardest problems. IP addresses can be spoofed. Tools can be shared. Languages in code can be faked. What we know for sure is how the malware works, not necessarily who is behind it.
That said, there are some consistent clues worth noting. The server used to deliver the malware contains what appears to be a Brazilian name and runs on HostGator Brasil, a Brazilian hosting company. The Ping_Net.dll module uses www.google.com.br specifically for its connectivity checks, not the international version. The command-and-control server routes through Synology’s free dynamic DNS service. Synology makes NAS devices, the kind people use at home to store files, and they offer a free hostname service that attackers are abusing here as their command infrastructure, pointing to IP 45.156.87.226 on port 7535. And throughout the malware code, the developer tag “Pjoao1578Developer” appears in the internal information of every single plugin. Pjoao appears to be a shortened form of a Portuguese given name. None of this is definitive. But the clues all point in the same direction.
There are also two typos that show up consistently across every version of this malware. The message terminator used in the command protocol is written as #Sucess# instead of #Success#. The command that delivers additional modules to the infected machine is written as RunBlugin instead of RunPlugin. In Portuguese, the word for success is sucesso. These are not random mistakes. They are the kind of errors a non-native English speaker makes consistently, and they show up in exactly the same form in version 2.6 and version 2.9, which means they have been in the codebase for a long time. What makes this particularly interesting is that the same typo appears not just in the protocol but also in the internal build path of the developer: the folder inside the compiled binary is literally named “Blugin Stub.” The same person who wrote the code also compiled it, and they made the same mistake in both places. The jump from 2.6 to 2.9 also tells you something: this is not a one-off experiment. Someone has been developing and improving this actively.
When the malware connects to its command server, it identifies itself with a fixed string: Desk||||||||2.9.0.0|| — that specific format is consistent across samples and can be used for network-level detection regardless of what server address the attacker is using at any given moment.
A cracked version of the DesckVB builder at version 2.6 is circulating freely. Attackers with minimal skills can deploy this today without writing a single line of code. Active samples are already at version 2.9, which means development has been ongoing. The gap between those two versions is not small. This is not a proof-of-concept sitting in a researcher’s lab. It is a working tool that is being actively maintained and distributed.
Here is what to look for if you want to detect this.
→ Watch for wscript.exe or cscript.exe dropping files into
C:\Users\Public. That folder is easy to overlook and was specifically chosen by this malware for exactly that reason.→ Alert on InstallUtil.exe being run by anything other than a known software installation process. A normal Windows machine running business software has no reason to run InstallUtil.exe on its own.
→ Flag PowerShell that loads .NET code directly into memory from a list of numbers. The specific pattern here is PowerShell building and loading an assembly from decimal-encoded data, which is not something that happens in normal system activity and stands out clearly in endpoint detection logs.
→ Look for processes named Microsoft.exe running from unusual folders. Real Microsoft programs live in
C:\WindowsorC:\Program Files. A Microsoft.exe running from a temp folder or a user profile folder is not legitimate and should be investigated immediately.→ Block outbound connections on port 7535 if there is no reason for it. The secondary attacker communication channel specifically uses this port.
→ Monitor for encrypted traffic going to Synology dynamic DNS hostnames (mysynology.net) from regular workstations. A NAS device or file server might legitimately use that service. A regular office computer has no reason to.
→ Any outbound connection from a workstation to a dynamic DNS hostname on a non-standard port is worth investigating right away.
The mutex value hardcoded into every sample is nozgrb6ev4t4c7sc2hz7iwnnmmwahj54. A mutex prevents the malware from running more than one copy of itself at the same time. Finding this value on a machine is a reliable detection signal.
If any of these indicators appear in your environment, isolate the affected machine before doing anything else. Memory forensics is the only reliable way to investigate this, since almost nothing ends up on disk.
Understanding privilege escalation, post-exploitation, and how attackers use Windows’ own tools against you is exactly what I cover in my ethical hacking course. Including a full dedicated lesson on Windows LOLBins, which is exactly the technique DesckVB uses to stay hidden.
Hacking is not a hobby but a way of life.
Sources: ShadowOpCode — GitHub · PointWild LAT61 Team
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.