Infernal Twin Infernal Wireless V3 Automated Wireless Hacking
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
Hacking is not a hobby but a way of life!
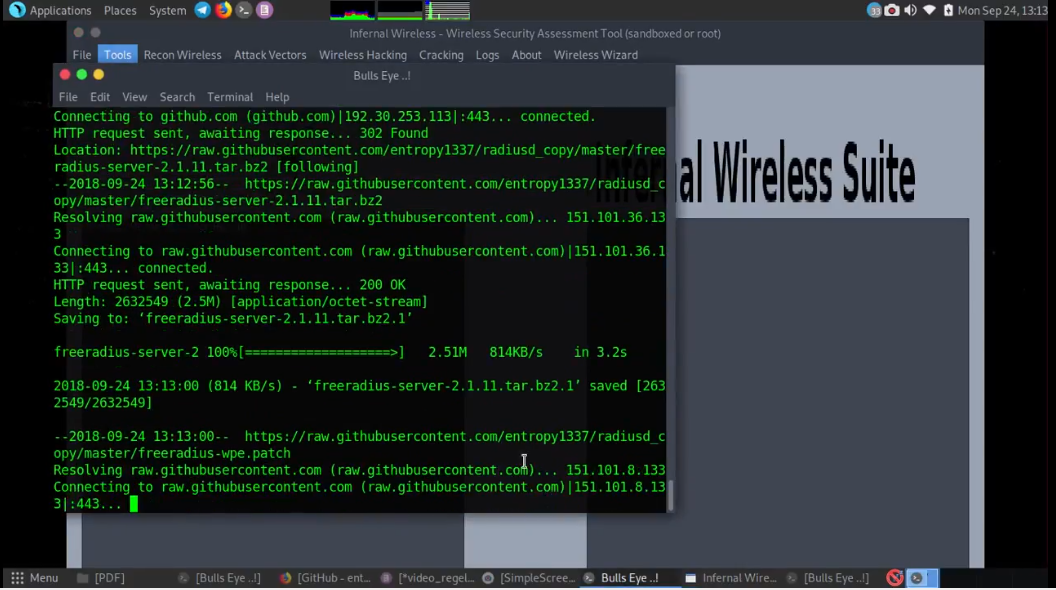
Infernal Twin is an automated wireless hacking suite written in Python which automates many of the repetitive tasks involved in security testing for wifi networks.
Infernal-Twin GitHub: https://github.com/entropy1337/infernal-twin
Features added and improved:
- Added BeeF XSS framework Integration
- Added HTTP Traffic View within tool
- Improved Infenral Wireless Attack
- Visual View of some of the panel improved
- Improved Basic Authentication during Social engineering assessment over wireless network
- Infernal-Wireless v2.6
This tool is created to aid the penetration testers in assessing wireless security. The author is not responsible for the misuse. All The Content Are Educational Purpose Only. Don’t Misuse This Tutorial. Hacking is illegal.
Infernal Twin, This was my third video. The date was Sept 24, 2018, when I publish this video on YouTube.
Video Infernal Twin
Become a member on Odysee.com
Earning on Odysee for watching videos ♥️
Here an invitation link, so that we both benefit.
In this way, you also support my work.
https://odysee.com/$/invite/@hackingpassion:9
WANT TO SUPPORT THE WEBSITE
Dear people, I do a lot of things on the Internet and I do it all for free. If I don’t get enough to support myself, it becomes very difficult to maintain my web presence, which takes a lot of time, and the server costs also have to be paid. Your support is greatly appreciated.
Thanks guys ..!
https://paypal.me/hackingpassion
Use the link above to donate via PayPal.
IMPORTANT THINGS TO REMEMBER
✓ This Video and Article is made for educational purposes and pentest only.
✓ You will not misuse the information to gain unauthorized access.
✓ This information shall only be used to expand knowledge and not for causing malicious or damaging attacks…!
Read also the Disclaimer
All the techniques provided in the tutorials on HackingPassion.com, are meant for educational purposes only.
If you are using any of those techniques for illegal purposes, HackingPassion.com can’t be held responsible for possible lawful consequences.
My goal is to educate people and increase awareness by exposing methods used by real black-hat hackers and show how to secure systems from these hackers.
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.