mosint An automated email OSINT tool

Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
Hacking is not a hobby but a way of life!
MOSINT is an OSINT Tool for emails. It helps you gather information about the target email. This is such as telephone numbers, data leaks, related domain names and much more.
Information Gathering
Information Gathering is the act of gathering different kinds of information against the targeted victim or system. There are various tools, techniques, and websites, including public sources such as Whois, nslookup that can help gather information. MOSINT is very helpful to gather information about all kinds of emails.
Main features
- Verification Service { Check if email exist }
- Check social accounts with Socialscan
- Check data breaches
- [need API] Find related emails
- Find related phone numbers
- Find related domains
- Scan Pastebin Dumps
- Google Search
- DNS Lookup
OSINT
OSINT stands for Open Source Intelligence that refers to the collection of data from the available public sources. Hackers use OSINT to perform social engineering and gather information on their targets and attack. Cyberstalkers use OSINT to track and exploit their targets.
Data breaches
“A data breach is a security violation in which sensitive, protected or confidential data is copied, transmitted, viewed, stolen or used by an individual unauthorized to do so.”
A data breach occurs when a hacker gains access to the database of a service or company which contains users’ private information. This information can range from usernames and passwords to social security numbers, addresses and even payment details. These lists are then usually sold online to criminal groups who seek to use this information for profit.
DNS lookup
In computer networks, a reverse DNS lookup or reverse DNS resolution is the querying technique of the Domain Name System to determine the domain name associated with an IP address – the reverse of the usual “forward” DNS lookup of an IP address from a domain name.
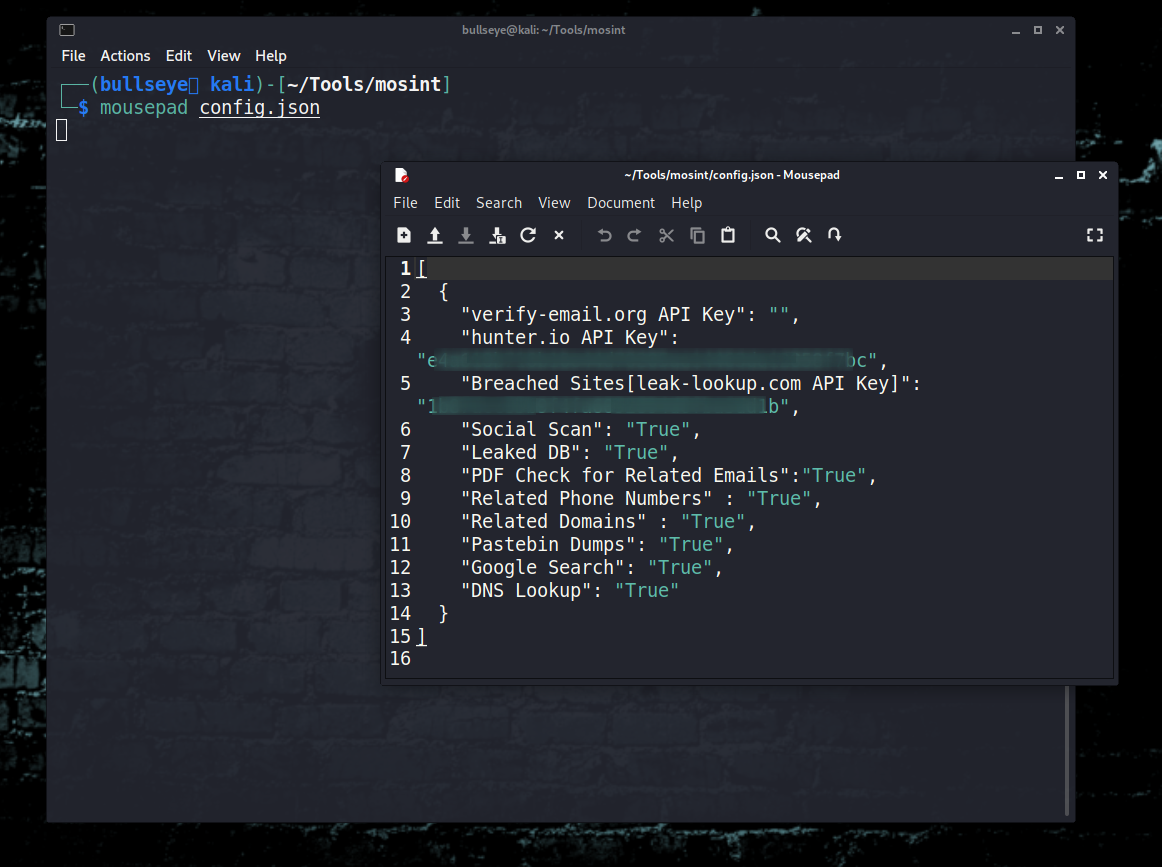
config files
You can turn features on off from the config.json
(In the video I show you in detail how you can get these APIs.)
| |
APIs:
[not required to run the program]
| Service | Function | Status |
|---|---|---|
| verify-email | Email Verification | ✅ 🔑 |
| hunter.io - Public | Related Emails | ✅ 🔑 |
| leak-lookup | Breached Sites Names | ✅ 🔑 |
| scylla.sh | Database Leaks | ✅ |
| hackertarget | DNS Lookup | ✅ |
| psbdmp | Pastebin Dumps | ✅ |
🔑 - API key required
For Use:
Save your API key in the config.json
Installation
Clone and install oneline
| |
Cloning the repository
| |
| |
| |
- You can edit the
config.jsonfile
Using
| |
- Set Target Email
| |
Also, you can exit by pressing the q key.
Tested on:
- Kali Linux
- Parrot OS
- MacOS (without SocialScan module)
List of Valid and Invalid Email Addresses
RFC-compliant email address validation List of Valid and Invalid Email Addresses.
This test suite comes from Dominic Sayers and is a mix of RFC examples and examples from other validators.
The test suite is currently allowing addresses that are unroutable on the public Internet, such as first. last@example. 123. This behavior is disabled by default, but can be switched on; the tests are run in both modes for comparison.
Here you can find the mosint script
video
Maigret In this video I show you how to install and use .. Besides that I always get a lot of questions about “problem solving”. In this video I show you how to deal with installation errors and how to install various pip3 scripts.
This time just music again.! .. No more talking … I want to remind you that there is a volume button on your computer.
Become a member on Odysee.com
Earning on Odysee for watching videos ♥️
Here an invitation link, so that we both benefit.
In this way, you also support my work.
https://odysee.com/$/invite/@hackingpassion:9
WANT TO SUPPORT THE WEBSITE
Dear people, I do a lot of things on the Internet and I do it all for free. If I don’t get enough to support myself, it becomes very difficult to maintain my web presence, which takes a lot of time, and the server costs also have to be paid. Your support is greatly appreciated.
Thanks guys ..!
https://paypal.me/hackingpassion
Use the link above to donate via PayPal.
IMPORTANT THINGS TO REMEMBER
✓ This Video and Article is made for educational purposes and pentest only.
✓ You will not misuse the information to gain unauthorized access.
✓ This information shall only be used to expand knowledge and not for causing malicious or damaging attacks…!
Read also the Disclaimer
All the techniques provided in the tutorials on HackingPassion.com, are meant for educational purposes only.
If you are using any of those techniques for illegal purposes, HackingPassion.com can’t be held responsible for possible lawful consequences.
My goal is to educate people and increase awareness by exposing methods used by real black-hat hackers and show how to secure systems from these hackers.
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.