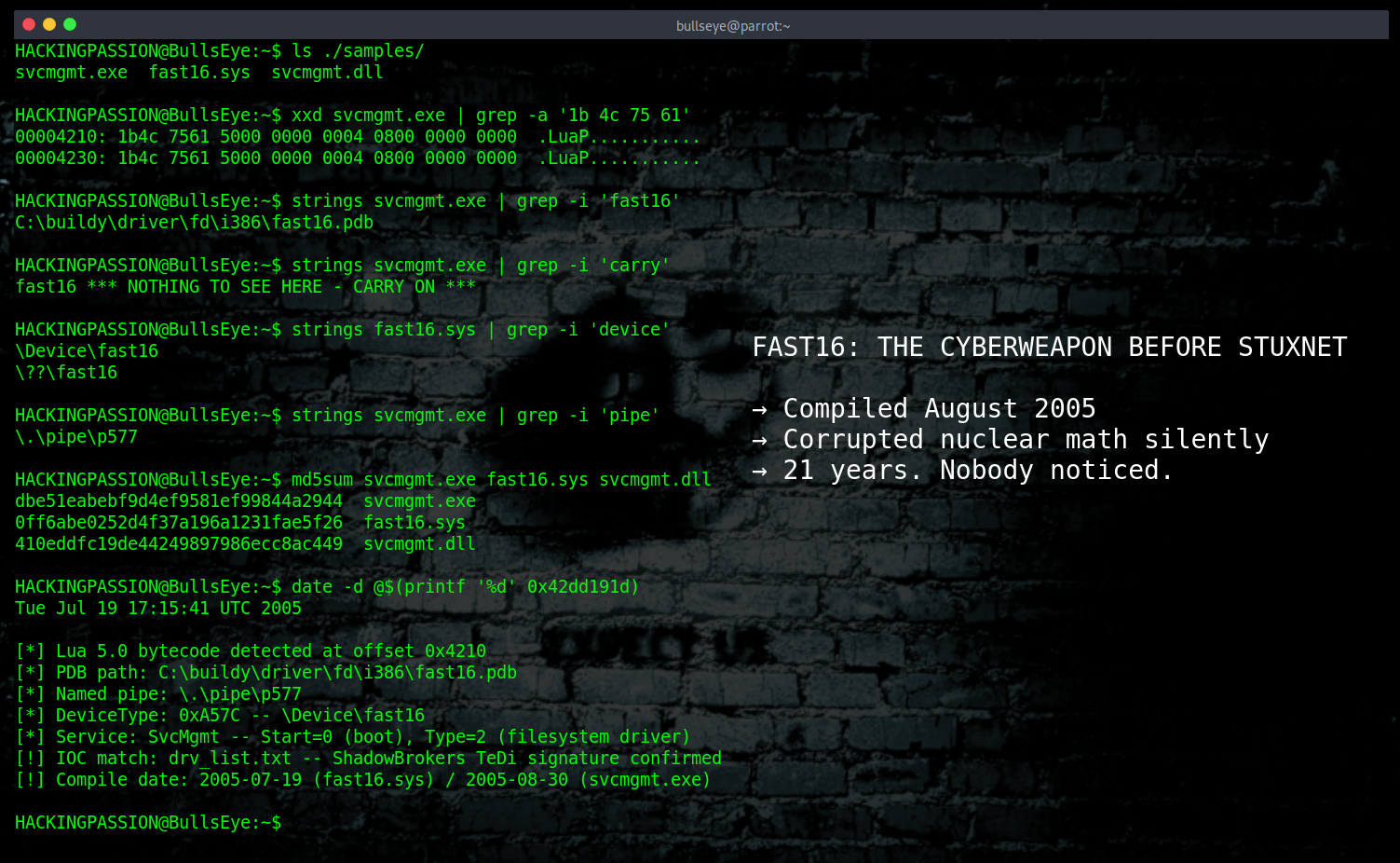
Fast16: The Cyberweapon That Predates Stuxnet by Five Years
For 21 years, a cyberweapon called fast16 sat completely undetected. This one did not destroy machines or blow things up. It corrupted the math. Scientists running nuclear and engineering simulations got output that looked completely normal, every number added up, every result made sense, and all of it was deliberately wrong. It surfaced last week. It predates Stuxnet by five years.
SentinelOne researchers Vitaly Kamluk and Juan Andrés Guerrero-Saade presented the full analysis of fast16 at Black Hat Asia last week. Fast16’s core binary has a compilation timestamp of August 30, 2005. Stuxnet’s C&C infrastructure was set up in November that same year.