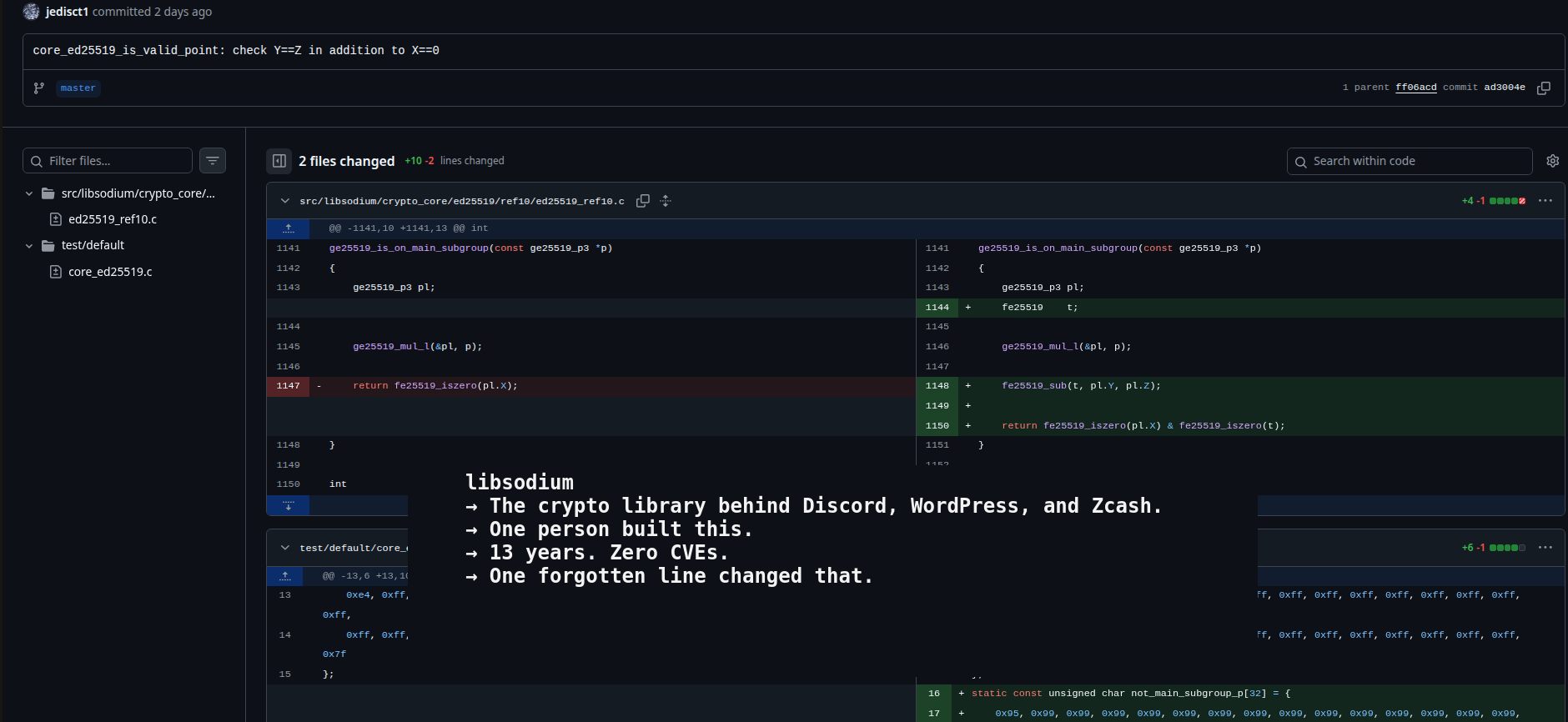
libsodium Gets First CVE After 13 Years: The Two-Line Fix
The crypto library behind Discord, WordPress, and Zcash just got its first CVE. After 13 years. 😏 libsodium. You’ve probably never heard of it. But it’s everywhere.
libsodium is one of the most trusted cryptographic libraries in the world. Discord secures voice chat with it. WordPress validates updates with it. Zcash processes transactions with it. Stellar powers financial apps with it.
13,300+ GitHub stars. Bindings in every programming language you can think of. From PHP to Rust to Python to Go.