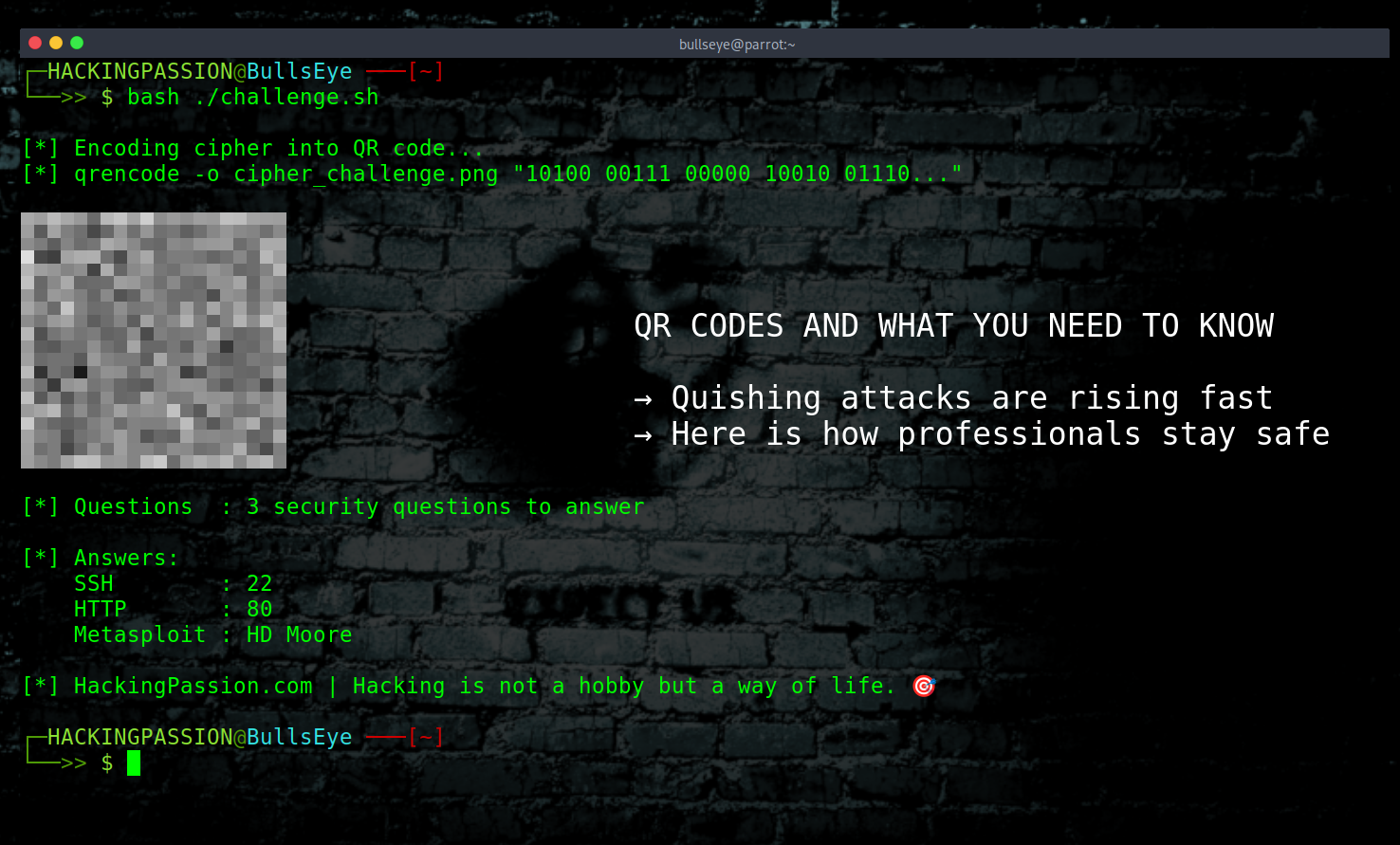
QR Codes: What You Need to Know
Yesterday, I posted a QR code challenge on this Ethical Hacking page, and it has since been removed. A cipher, hidden inside a QR code, with three security questions and a prize. The comments that followed gave me a good reason to write about this, because this is a topic that deserves a proper explanation.
The comments came in fast. “You should never scan a random QR code.” “This is a trap.” “You failed the first part just by scanning.” “Hackers know better than to do this.” And honestly, that reaction makes sense. You see a QR code on a hacking page, you do not know what is inside it, and being careful is right. But being careful does not mean refusing to engage. It means knowing how to approach it.