Shodan Eye Getting Started With Shodan
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
Hacking is not a hobby but a way of life!
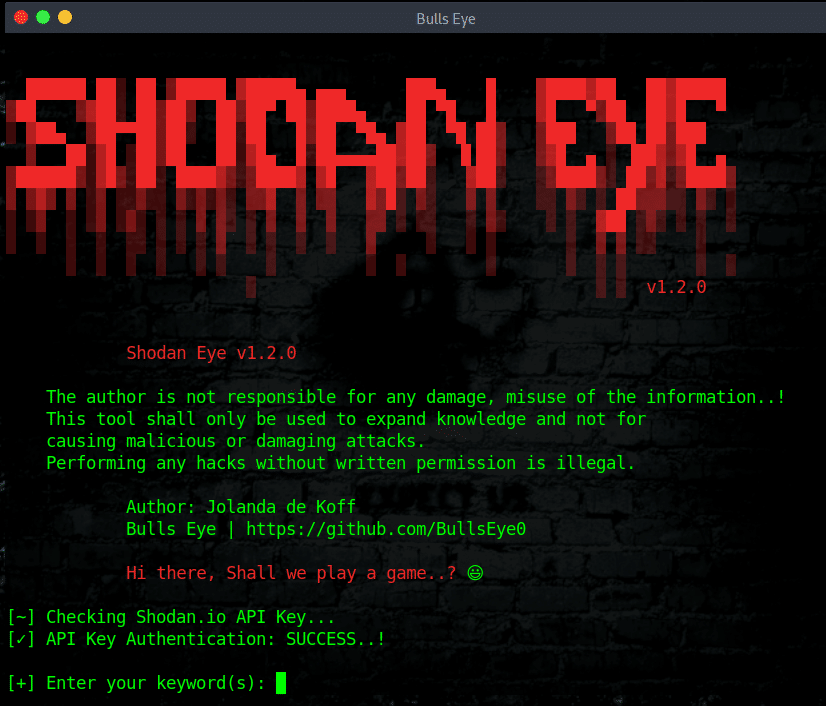
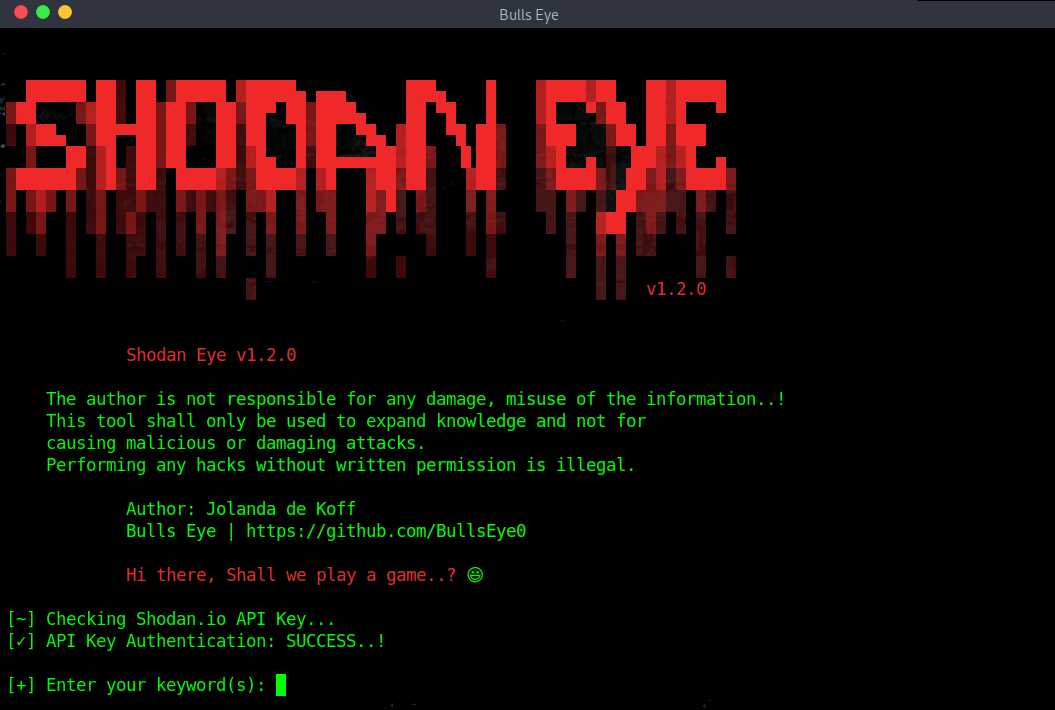
Shodan Eye collects and returns all information about every device that is directly connected to the internet and according to the keywords you entered.
What type of devices can be found with Shodan Eye
The types of devices that are indexed can vary enormously. It can be from small desktops to refrigerators or either nuclear power plants, webcams, water treatment facilities, coffee machines, yachts, medical devices, traffic lights, wind turbines, license plate readers, smart TVs and much more. Actually we can say everything you could possibly imagine that’s plugged into the internet.
Here you can find the latest post-upgrade about Shodan Eye
Connected devices
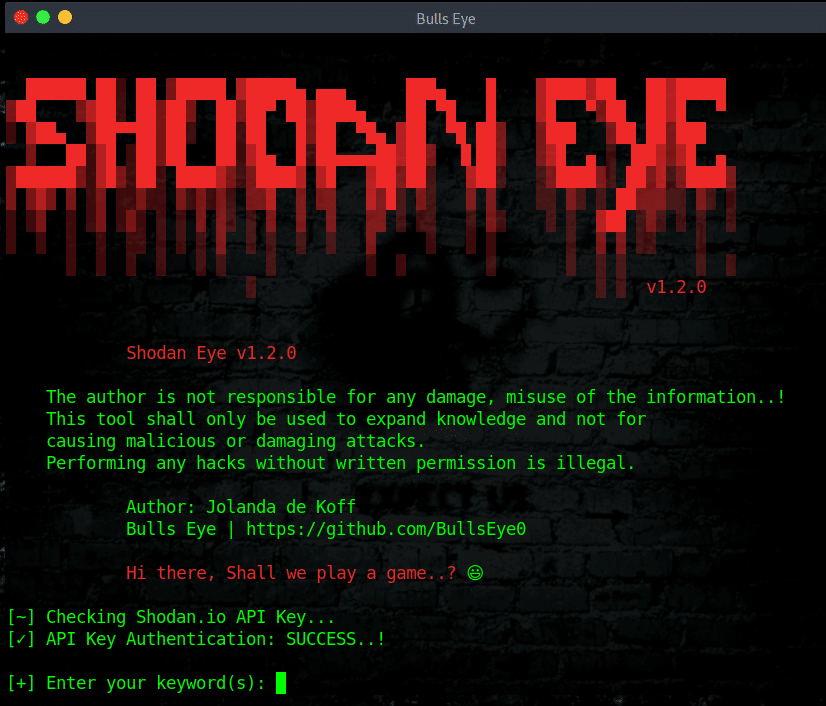
There are already over 10 billion connected devices active today, and that figure is expected to reach 64 billion by 2025. Shodan runs its scans 24/7, ensuring all its data is up to date. Shodan has picked up support for IPv6 addresses, but you won’t see those as often you can see IPv4.
Shodan error
Shodan Dorks
With Shodan Eye, you can find everything using “your own” specified keywords. Shodan queries examples can be found in the file attached in the Github repository named Shodan_Dorks_The_Internet_of_Sh*t.txt
The information obtained with Shodan Eye can be applied in many areas such as:
- Network security, keep an eye on all devices in your company or at home that is connected to the internet
- All sort off vulnerabilities
WHAT IS SHODAN?
It is a search engine that lets the user find specific types of computers (webcams, routers, servers, etc …) currently connected to the internet using a variety of filters. Some have also described it as a search engine of service banners, which are metadata that the device sends back to the client.
Shodan the scariest search engine on the internet
Shodan terrifies non-technical people who don’t understand how the internet works. CNN called Shodan the “Scariest search engine on the internet” in 2013. This is definitely of no sense since attackers intent on causing harm don’t need Shodan to find targets.
Beware of the attacks on your own devices!
A quick search for the term “default password” reveals countless printers, servers and system control devices that use “admin” as their user name and “1234” as their password. In many cases, it doesn’t even have a password, and you leave it blank. Until today, many connected systems require no credentials at all!
WHAT IS THE DIFFERENCE BETWEEN GOOGLE OR ANOTHER SEARCH ENGINE?
The most fundamental difference is that Shodan Eye analyzes the Internet, while Google analyzes the World Wide Web. Moreover, the devices connected to the World Wide Web are only a small part of what is really connected to the Internet.
Shodan error
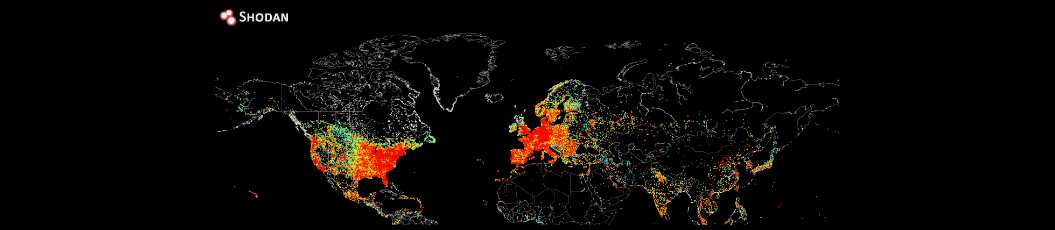
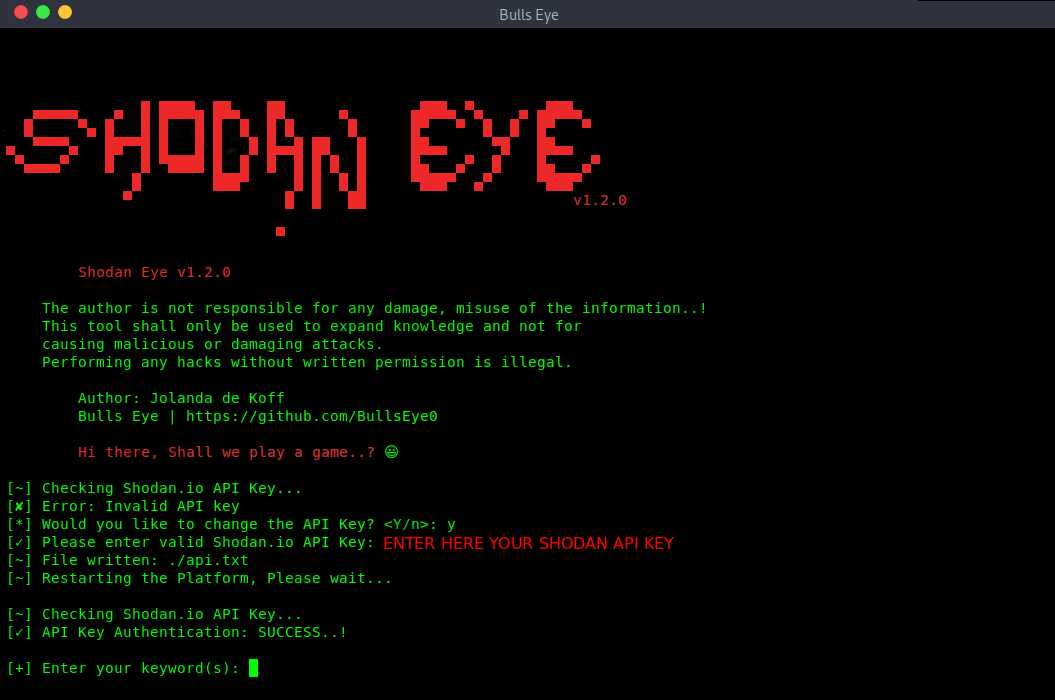
SHODAN API KEY
For additional data gathering, you can enter a Shodan API key when prompted. A Shodan API key can be found here. Once your account has been confirmed you will receive your own API Key.
Shodan error
Pay attention
Make sure that your Shodan API key you are entering is valid. I personally recommended to take out a paid subscription, but however a free account is sufficient to do a lot of things.
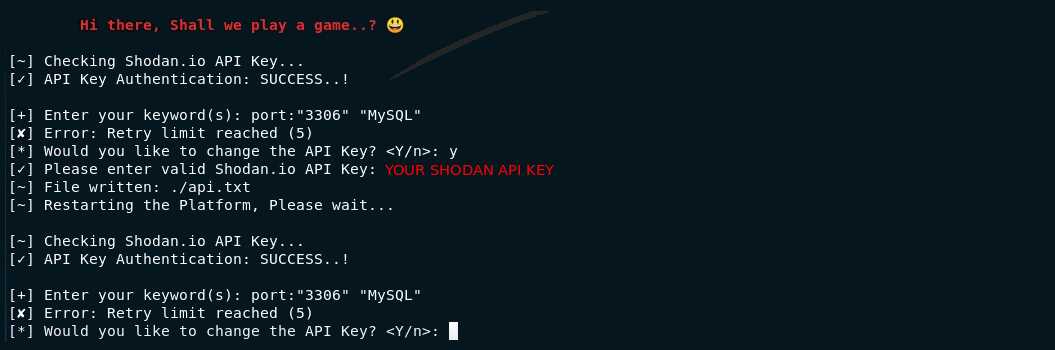
Shodan error
The current version of Shodan Eye use Python 2.7 but another version using Python 3 is scheduled.
Shodan error
Shodan error
Install Shodan Eye on Linux
| |
| |
| |
Use Shodan Eye
| |
After entering the above command you will be prompted to enter your Shodan API Key. That’s all, it’s now the time for you to enjoy. For more information please feel free to visit the Github repository.
Shodan Eye Video
Here is a brief summary of what Shodan Eye can do.
Shodan Eye Ethical Hacking Tool Release 2020
Become a member on Odysee.com
Earning on Odysee for watching videos ♥️
Here an invitation link, so that we both benefit.
In this way, you also support my work.
https://odysee.com/$/invite/@hackingpassion:9
WANT TO SUPPORT THE WEBSITE
Dear people, I do a lot of things on the Internet and I do it all for free. If I don’t get enough to support myself, it becomes very difficult to maintain my web presence, which takes a lot of time, and the server costs also have to be paid. Your support is greatly appreciated.
Thanks guys ..!
https://paypal.me/hackingpassion
Use the link above to donate via PayPal.
IMPORTANT THINGS TO REMEMBER
✓ This Video and Article is made for educational purposes and pentest only.
✓ You will not misuse the information to gain unauthorized access.
✓ This information shall only be used to expand knowledge and not for causing malicious or damaging attacks…!
Read also the Disclaimer
All the techniques provided in the tutorials on HackingPassion.com, are meant for educational purposes only.
If you are using any of those techniques for illegal purposes, HackingPassion.com can’t be held responsible for possible lawful consequences.
My goal is to educate people and increase awareness by exposing methods used by real black-hat hackers and show how to secure systems from these hackers.
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.