Hfish a Honeypot Platform
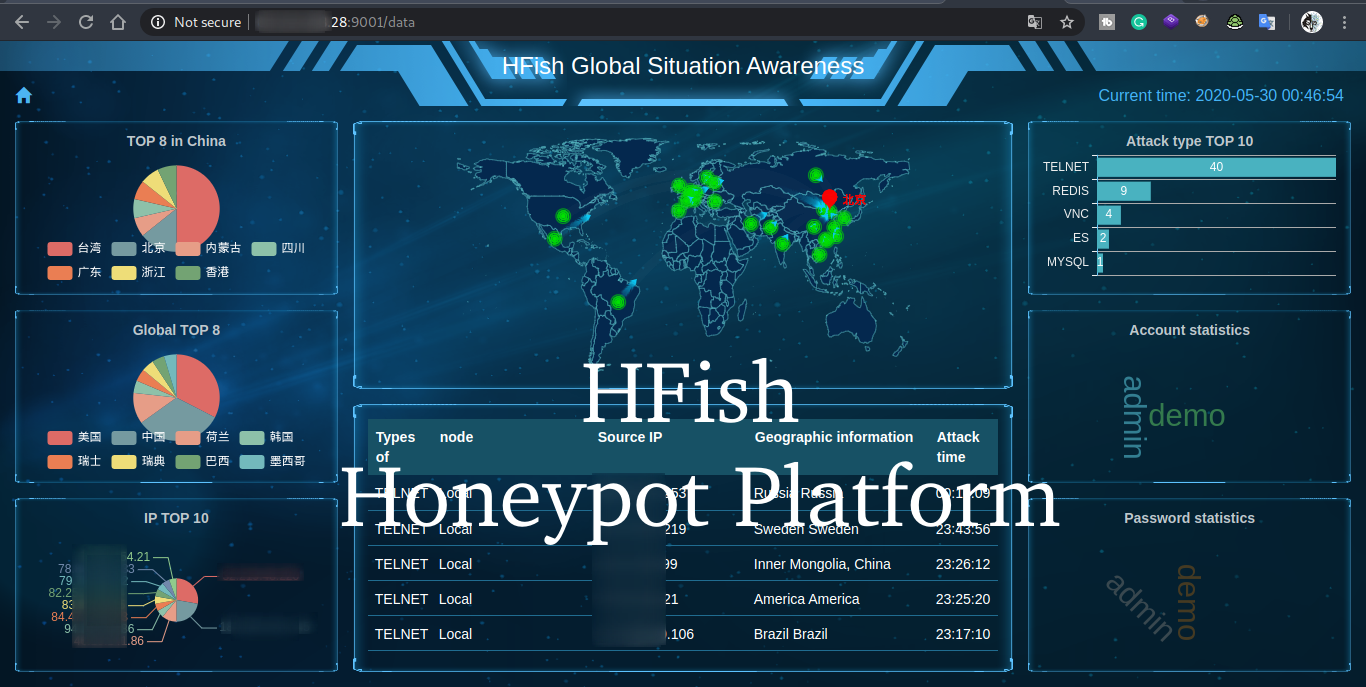
HFish Honeypot In this article and video, I show you how to set up the HFish Honeypot in a few different ways and show you what you can do with it. HFish It is a cross-platform honeypot platform developed based on Golang, which has been meticulously built for enterprise security.
What I show in this article and video
- For this article, I set up an own VPS server.
- How you can easily set up an Ubuntu Server (VirtualBox) and put up the Honeypot
- How to use “Play with Docker” to test the honeypot for several hours
- How to attack your own honeypot, using an anonymous tool.
- Some more
What is a Honeypot
A honeypot looks like a real computer system that deliberately presents itself as vulnerable with applications and data, fooling cybercriminals into thinking it’s a legitimate target. For example, for (worm) viruses and customer billing systems - a frequent target of attack for criminals who want to find credit card numbers. The system is made as vulnerable as possible. If the hackers are in, they can be tracked, and their behavior assessed for clues on how to make the real network more secure.
Honeypots are also used to realize post-admission control in quarantine networks. Sometimes a honeypot is used to retrieve the hacker’s data. This way they can arrest the hacker and if necessary try it. The data retrieved by honeypot will then serve as proof.
A honeypot will have information that a hacker finds interesting, such as password information. In my own experience, this list can be a lot of fun and big, but also a lot of the most chosen passwords such as admin and 123456

What about the name “Honeypot”
The origin of the term “honeypot” (honey jar) is often associated with the bear Winnie the Pooh, who ended up in all kinds of situations because of his great love for pots of honey.
Another is
Honeypot comes from the world of espionage, where Mata Hari-style spies who use a romantic relationship as a way to steal secrets are described as setting a “honey trap” or “honeypot”. Often, an enemy spy is compromised by a honey trap and then blackmailed to hand over everything he/she knows.
- Multi-function: Not just support
HTTP(S)Pot,It also supportsSSH、SFTP、Redis、Mysql、FTP、Telnet、Deepetc. - Expansibility: Provide
APIInterface,Users can expand honeypot module at will (WEB、PC、APP) - Convenience: Use Golang Development, Users can
Win+Mac+LinuxQuickly deploy a honeypot platform on
HFish Support honeypot
SSHPotRedisPotMysqlPotMemCachePotTelnetPotFTPPotWEBPotDeepPotHTTPPotTFTPPotVNCPotESPotCustomPot- And some more
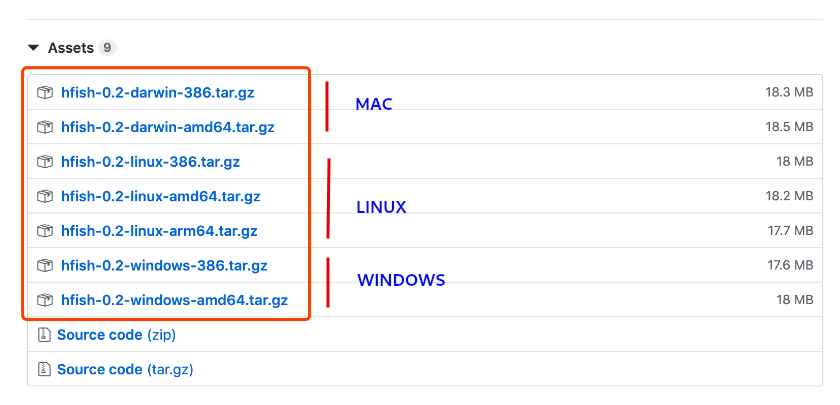
HFish can be installed on Linux, Windows, Mac and Raspberry Pi
- darwin for Mac version
- 386 is a 32 -bit system, amd64 is a 64 -bit system
- **arm64 **ARM architecture 64- bit can be used for Raspberry Pi
Unfortunately, because I see that entire articles are regularly copied from hackingpassion.com, and without even mentioning Hacking Passion and pretending it was written themself, I decided to stop copying on hackingpassion.com.
I know this can be very difficult, especially if you have to copy (large) pieces of code, or commands, freehand.
On the other hand, this is also a very good exercise. Because once you do it wrong the program usually doesn’t work. A very good way to learn. (I can definitely recommend doing this with everything) - just a really good exercise :-D
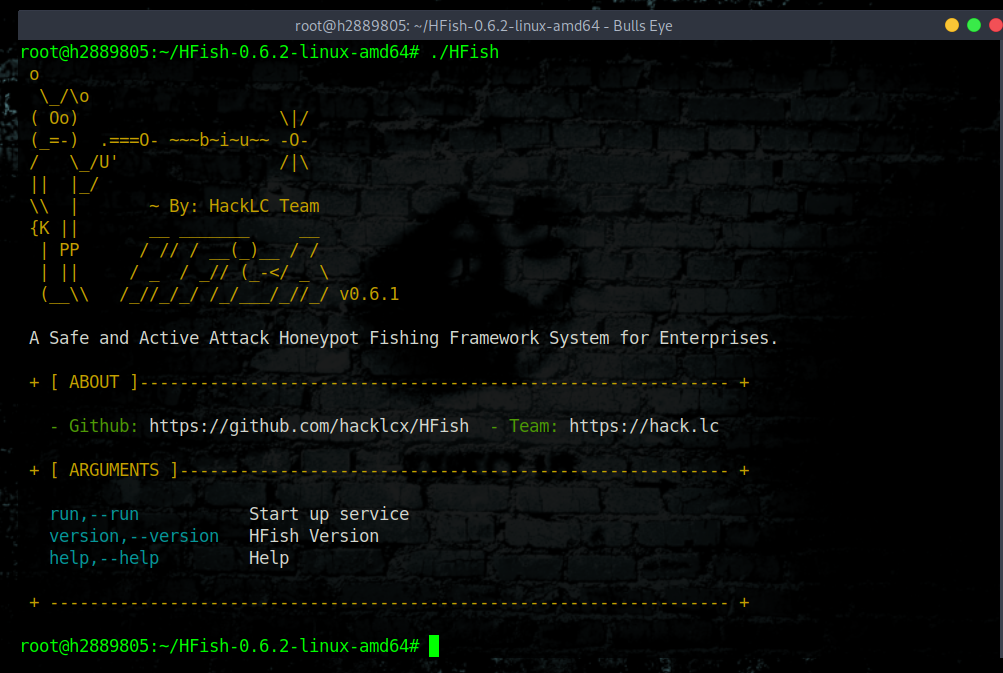
Install HFish on a Ubuntu Server
Both for this article and in the video I will show you how to install HFish on an Ubuntu server. How to install an Ubuntu Minimal server on, for example, a VirtualBox, I show you in detail in the video.
As soon as the Ubuntu server (You can of course use various Linux servers, such as a Debian or a Centos) We will start installing the Honeypot
Obviously you should check if you have the correct release. You can find it here.
|
|
|
|
|
|
|
|

To start the HFish Honeypot simply run:
|
|
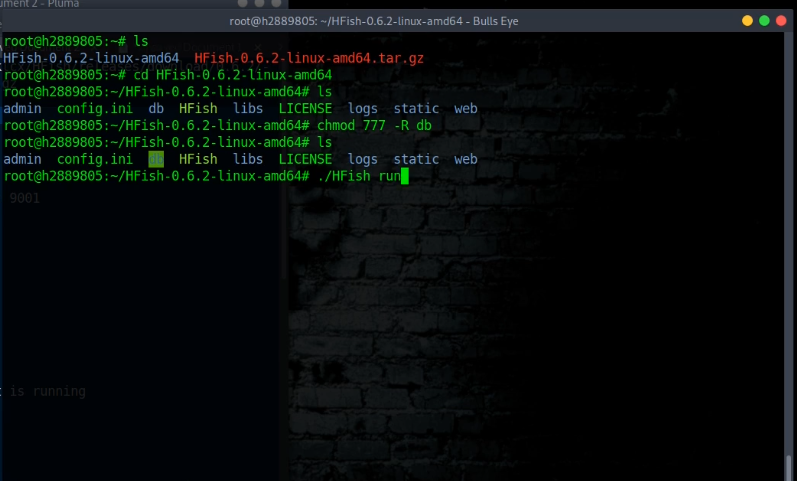
How to solve a crash problem with HFish and setup a cronjob
This is also very handy to just install the cronjob so that you can also work on your website or other things while the Honeypot continues to run. So I advise you to just use this.
After testing, because the concurrency is too high, and other scripting issues, the program will look abnormal, and causing the program process to exit.
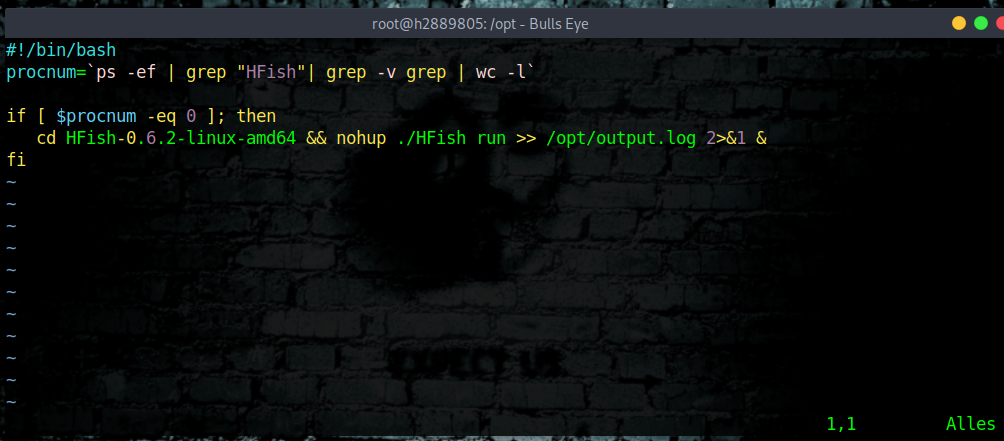
With the help of a bash script, we will address the cronjob, and in this way, we ensure that the script is controlled every minute by the cron that we are going to place.
Open a file with vim, nano or any other editor /opt/monitor.sh. In this example I use vim.
|
|
Place the following bash script in the terminal and save it. Make sure with this command that it will be the right version of HFish (in this tutorial I use HFish-0.6.2-linux-amd64) Make sure you change this in the script as well to the one you have downloaded.
|
|
The next thing we are going to do is create a cron job to make sure that (in this case) the script runs every minute so that HFish keeps running.
We open the cronjob with the following command:
|
|
And now we put the next cron line at the bottom, exactly as I show in the picture.
|
|
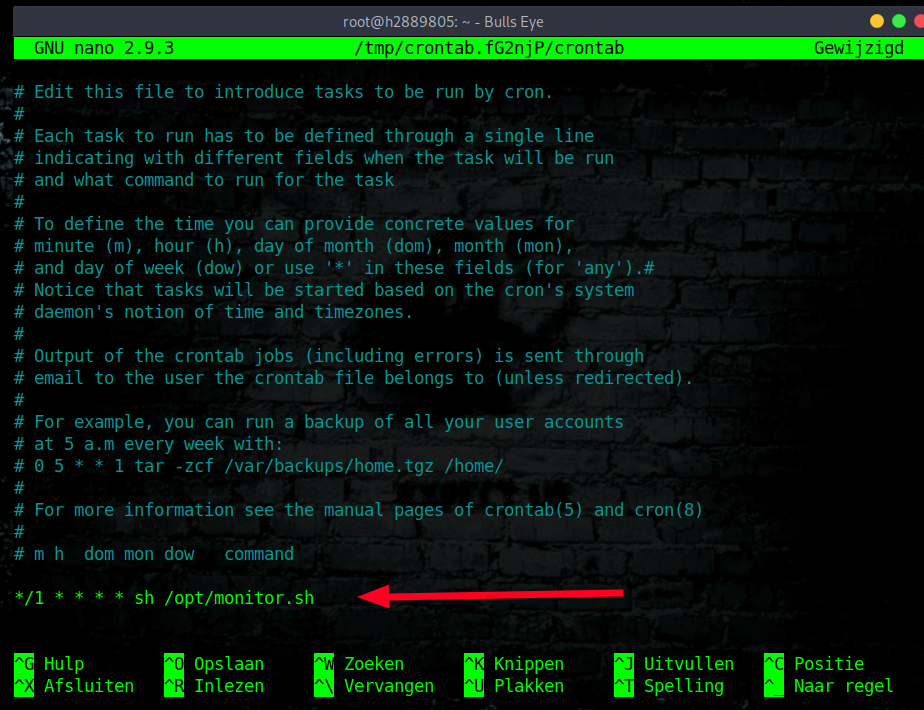
Write the content, execute once a minute : wq! (vim)
or
ctrl and O for (nano)
Save and exit.
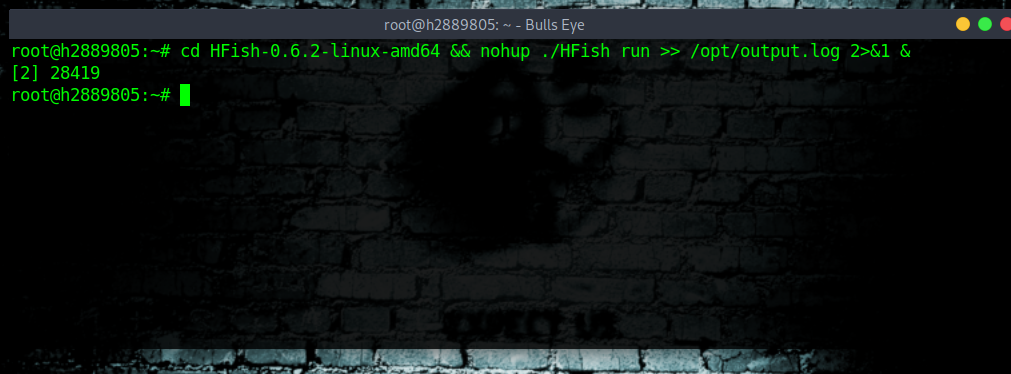
With the follow command we make sure the script will run without a stop.
|
|
As you see in this command we use “nohup”. Nohup runs a command that keeps running after you log out.
The output file you can find in /opt/output.log
Video HFish Honeypot
In this video, I will show you all sorts of things.
For example, how to install a simple Ubuntu server locally, how to install HFish, how to use Play with Docker. At the end of the video, I’ll show you what traffic there has been when the Honeypot runs for several hours.
I tried to indicate the commands as clearly as possible. In this video, I use my own VPS server. Attacks are not intended to take place here. Be polite to use your own (local) server for this. I hope you enjoy this video. If there have a comment, you can leave them at the bottom of this article, or on YouTube itself.
Most important have fun..! :-D
Become a member on Odysee.com
Earning on Odysee for watching videos ♥️
Here an invitation link, so that we both benefit.
In this way, you also support my work.
https://odysee.com/$/invite/@hackingpassion:9
Redis honeypot
redis-cli, the Redis command line interface
redis-cli is the Redis command-line interface, a simple program that allows sending commands to Redis, and read the replies sent by the server, directly from the terminal.
It has two main modes: an interactive mode where there is a REPL (Read Eval Print Loop) where the user types commands and get replies; and another mode where the command is sent as arguments of redis-cli, executed, and printed on the standard output.
The command I use in this example:
|
|
|
|
|
|
|
|
|
|
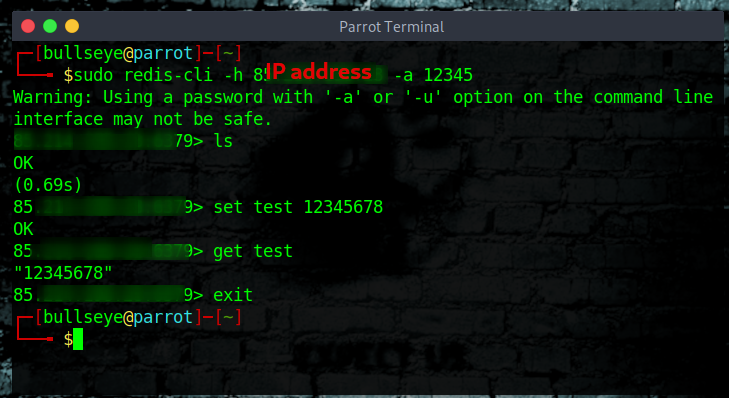
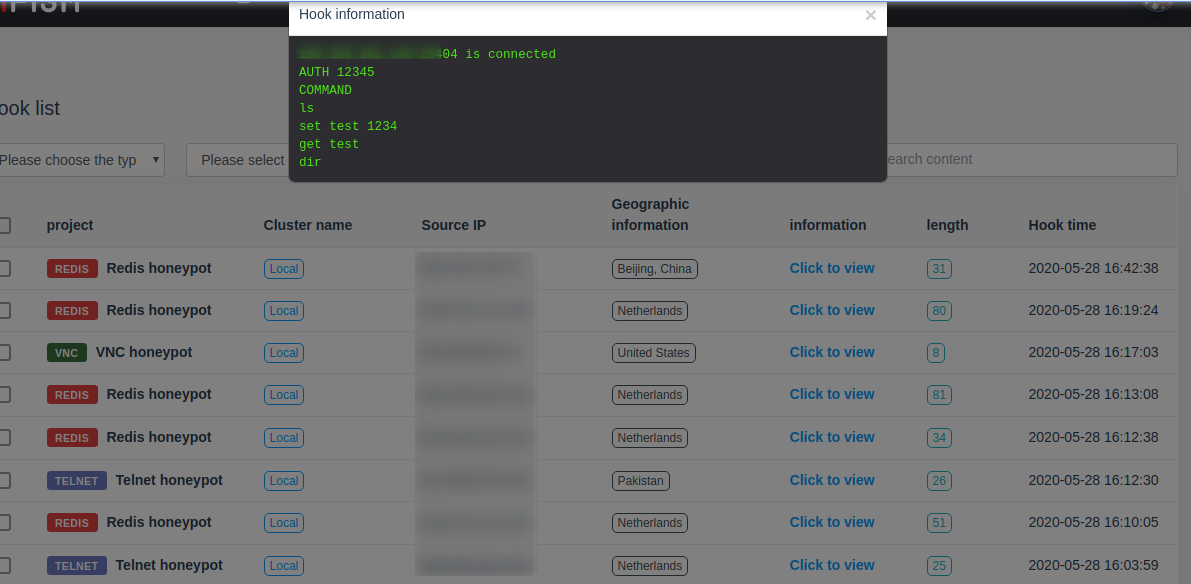
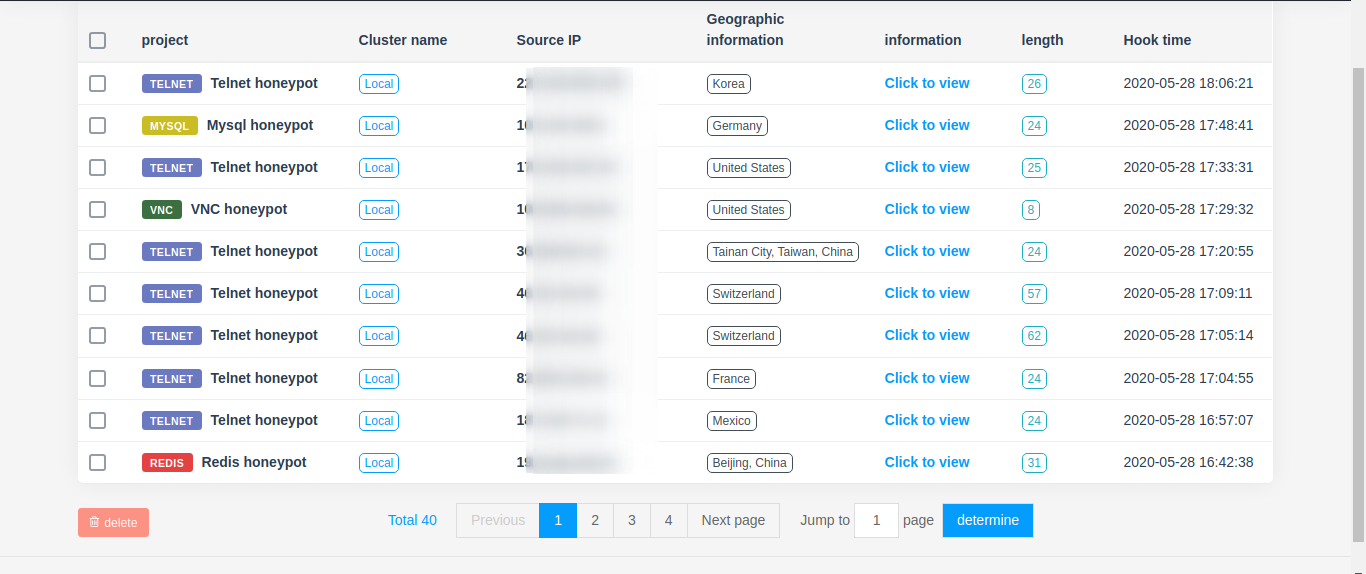
Press on “click to view” to see what the relevant IP address has done for an attack. So you can see various commands they have used.
Telnet honeypot
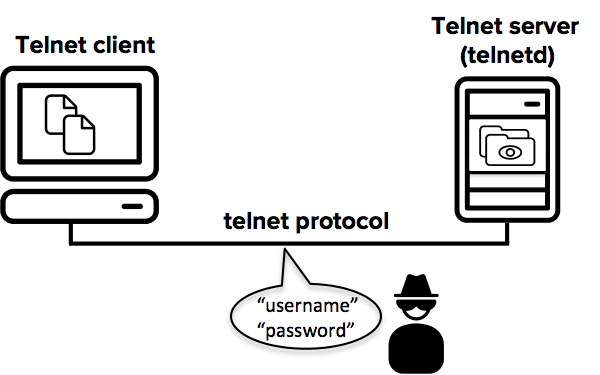
Telnet is one of the earliest remote login protocols on the Internet. The Telnet session between the client and the server is not encrypted. Anyone with access to the TCP/IP packet flow between the communicating hosts can reconstruct the data that flows between the endpoints and read the messaging, including the usernames and passwords that are used to log in to the remote machine.
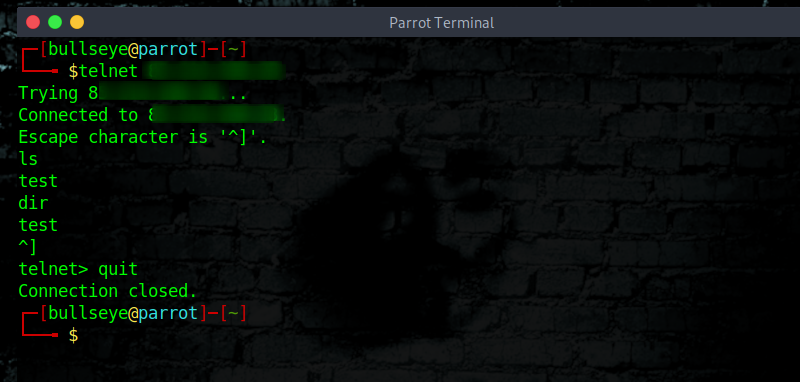
Telnet honeypot
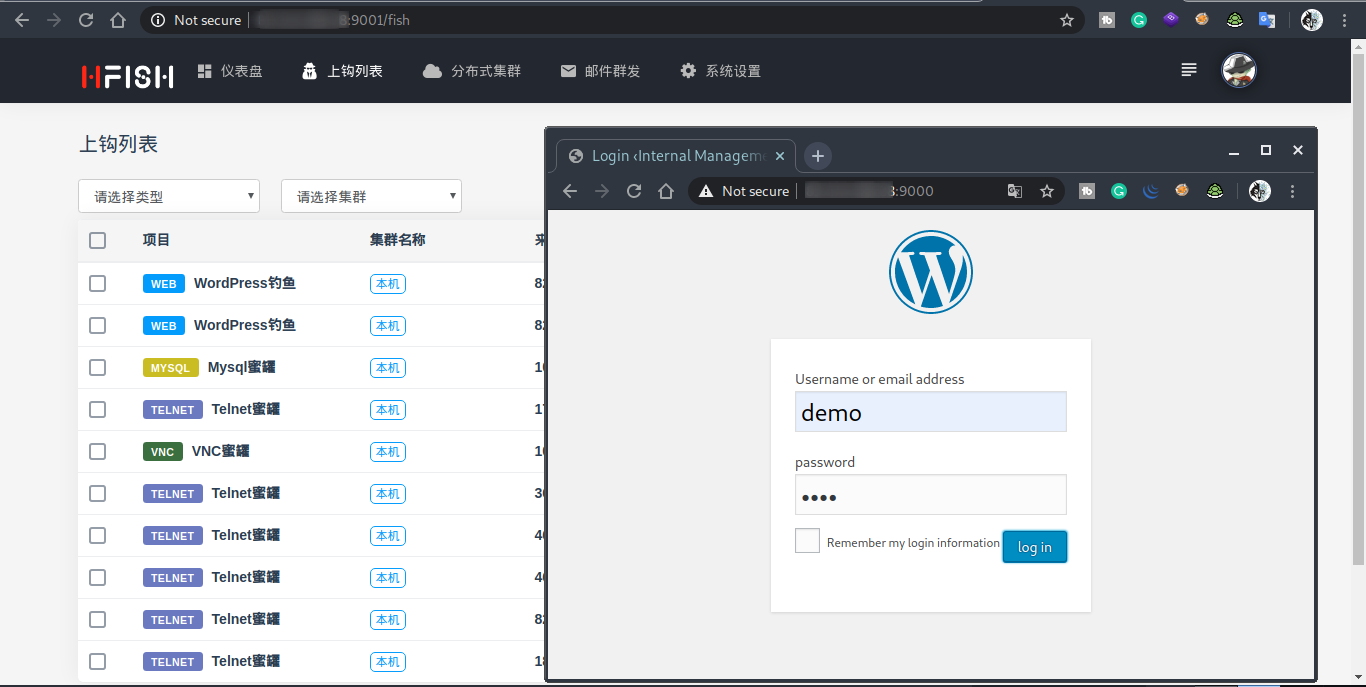
WEB honeypot WordPress
|
|
- status whether to start WEB
1start0shut down, start the API after WEB before reporting results - addr WEB server address, 0.0.0.0 is open to the outside world, 127.0.0.1 is open to the inside and can go through Nginx reverse proxy
- template template path
- index home page file
- static static file path Note: there must be two directories, HTML files and static files can not be same level
- url access path, the default
/can be changed to/index.html/index.asp/loginetc.
Play with Docker HFish Honeypot
Play with Docker (PWD) is a Docker playground that allows users to run Docker commands in a matter of seconds. It gives the experience of having a free Alpine Linux Virtual Machine in a browser, where you can build and run Docker containers and even create clusters in Docker Swarm Mode. Under the hood Docker-in-Docker (DinD) is used to give the effect of multiple VMs/PCs.

You can also use Play with Docker also for many other docker applications.
You may need to change the ssh port. In this example, I changed it to -p 2222:22. (Normal will this be 22:22)
Use the “ADD NEW INSTANCE” button to open a new terminal.
|
|
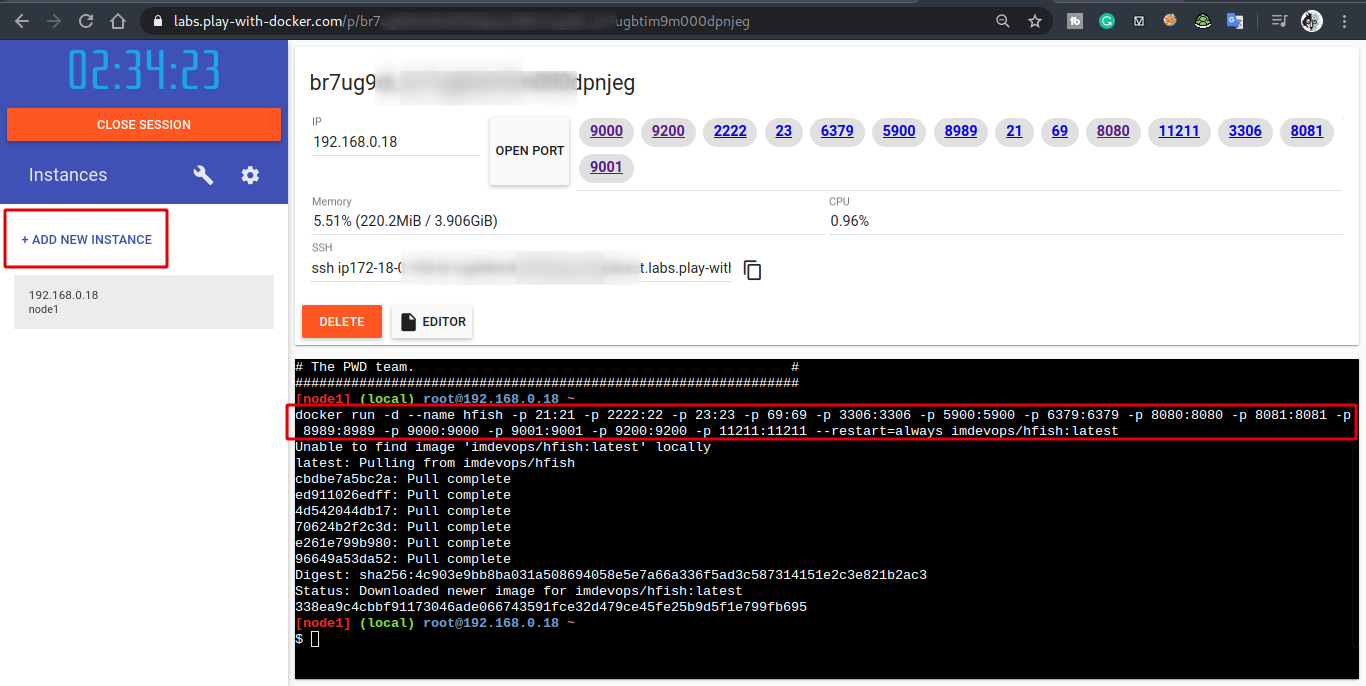
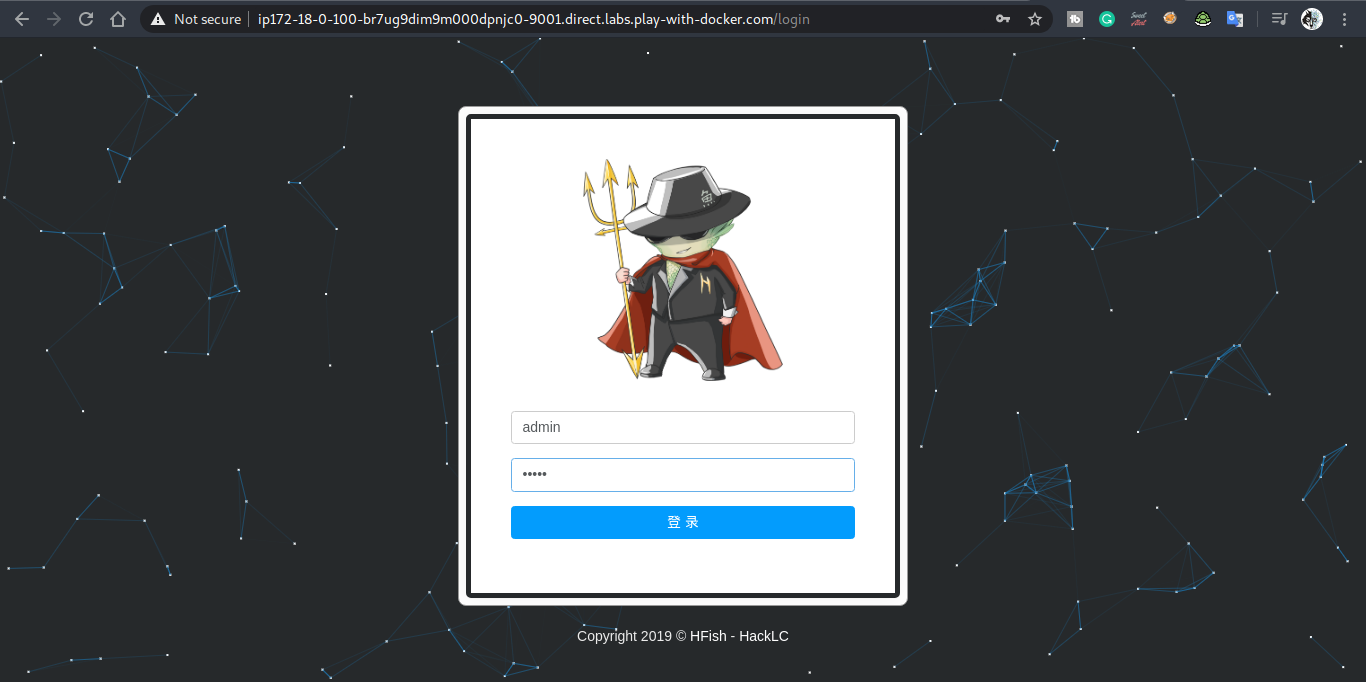
Use port 9001 to log in
The default login details are:
Username :: admin
Password :: admin
Conclusion
It was so much fun to make this video and article. I have been using honey pots for a long time. There are many different honeypots on the internet. HFish is one and HFish is a very nice option to use. I am sure that there will be more articles and videos about honeypots in the future.
I sincerely hope you enjoy this video and article as much as I did. :-)
WANT TO SUPPORT THE WEBSITE
Dear people, I do a lot of things on the Internet and I do it all for free. If I don’t get enough to support myself, it becomes very difficult to maintain my web presence, which takes a lot of time, and the server costs also have to be paid. Your support is greatly appreciated.
Thanks guys ..!
https://paypal.me/hackingpassion
Use the link above to donate via PayPal.
IMPORTANT THINGS TO REMEMBER
✓ This Video and Article is made for educational purposes and pentest only.
* You will not misuse the information to gain unauthorized access.
✓ This information shall only be used to expand knowledge and not for causing malicious or damaging attacks…!
Read also the Disclaimer
All the techniques provided in the tutorials on HackingPassion.com, are meant for educational purposes only.
If you are using any of those techniques for illegal purposes, HackingPassion.com can’t be held responsible for possible lawful consequences.
My goal is to educate people and increase awareness by exposing methods used by real black-hat hackers and show how to secure systems from these hackers.