XCTR Hacking Tools All in One Tool for Information Gathering
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
Hacking is not a hobby but a way of life!
XCTR Hacking Tools is a collection of great Tools: Dork Finder, Admin Panel Finder, Cms Finder, Reverse Ip, Page Viewer, and a Proxy Finder A Step-by-Step walkthrough..!
Sometimes you come across a tool that is worth mentioning. XCTR Hacking Tools is one of them. In this article and video, I show you the options and how to install this tool.
This tool is written by Hulya Karabag | Mert Beyoglu
Version 1.0.0 All in one tools for Information Gathering.
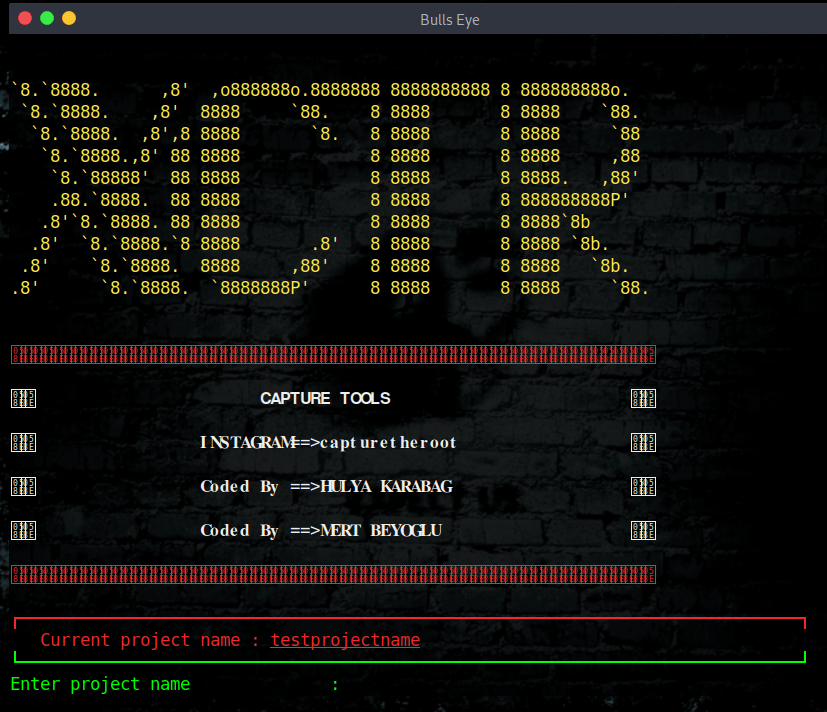
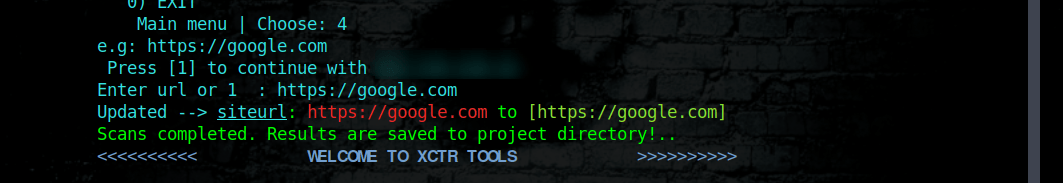
Initially, you need to create a project where you will save everything.
All of the collected information is saved as “project-name” in the results directory.
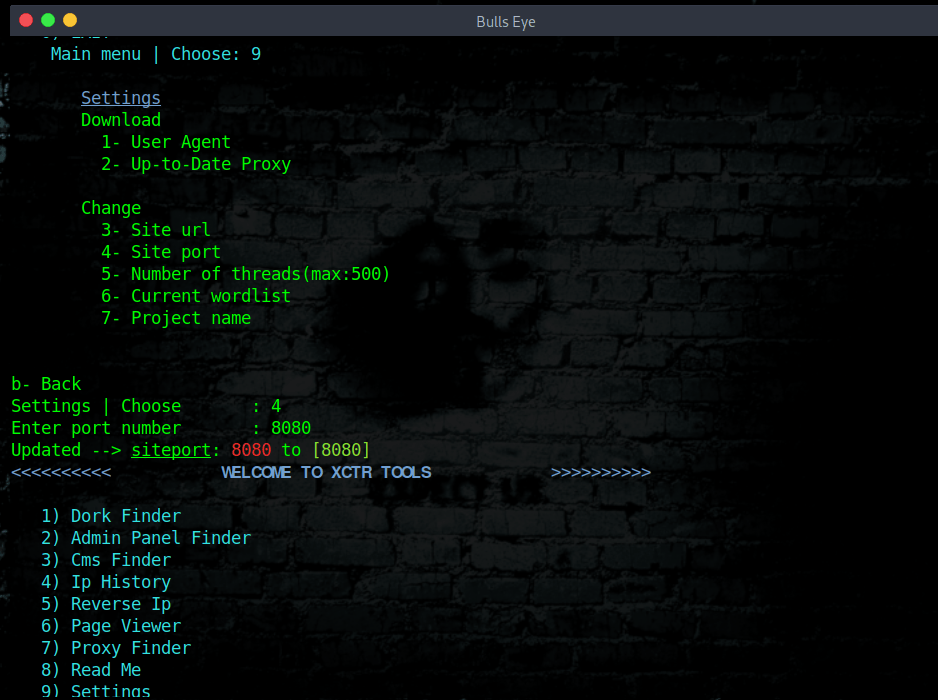
You can update user agent and proxy information in the settings section and also update URL, proxy, project name, wordlist, thread numbers.
Features
This tool includes a lot of intresting and amazing tools:
- Dork Finder
- Admin Panel Finder
- CMS Finder
- IP History
- Reverse IP
- Page Viewer
- Proxy Finder
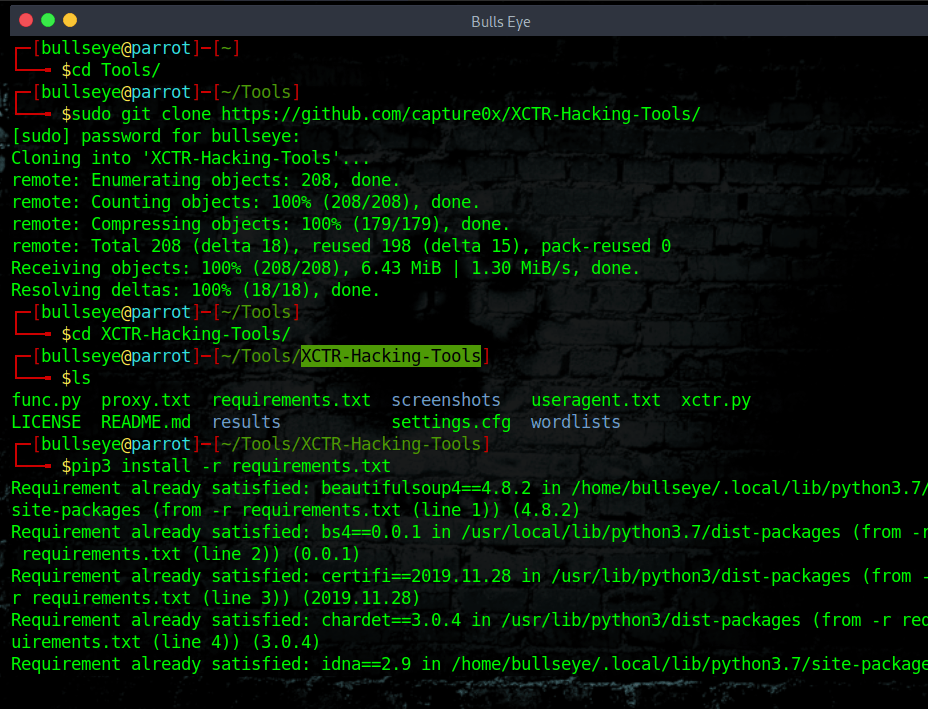
Installation
As you can see the XCTR Hacking Tools is very easy to set up.
| |
| |
| |
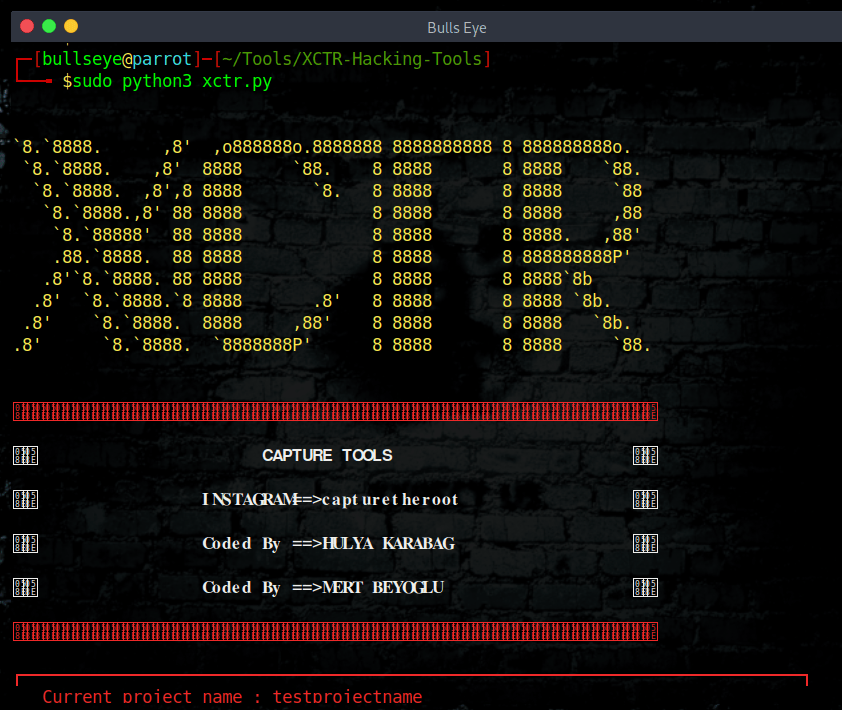
XCTR Hacking Tools Usage
| |
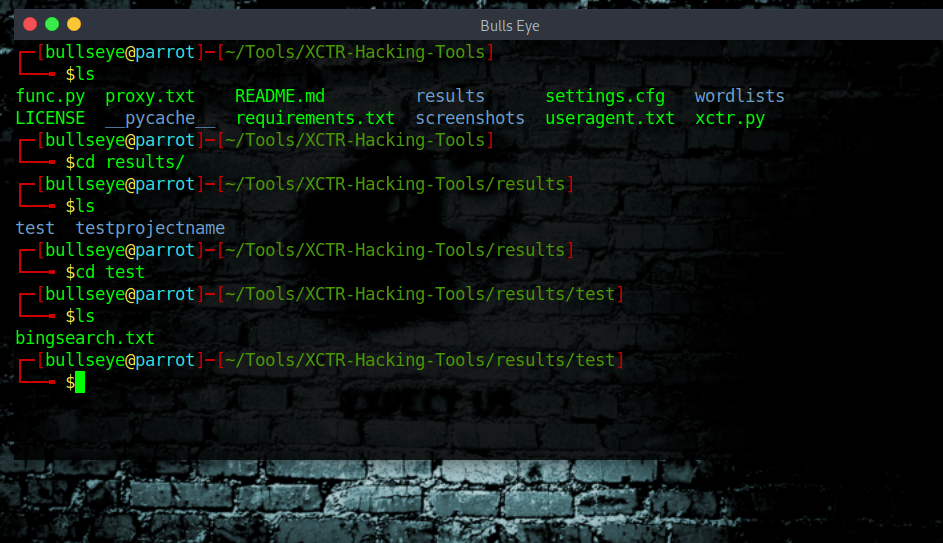
All results save in results/project-name.
XCTR Hacking Tools will save all the results in a project file as you can see in the image below.
“The Internet and search engine queries will start you on your journey. Learning and developing your capacity to learn independently is a huge step and part of that journey”
The XCTR Hacking Tools
Dork Finder 😍
https://github.com/capture0x/XCTR-Hacking-Tools#dork-finder
The dork finder have 2 section. Bing and yandex.
e.g:
| |
Yandex - Yandex I personally didn’t know this Search Engine. Nice to discover something new.
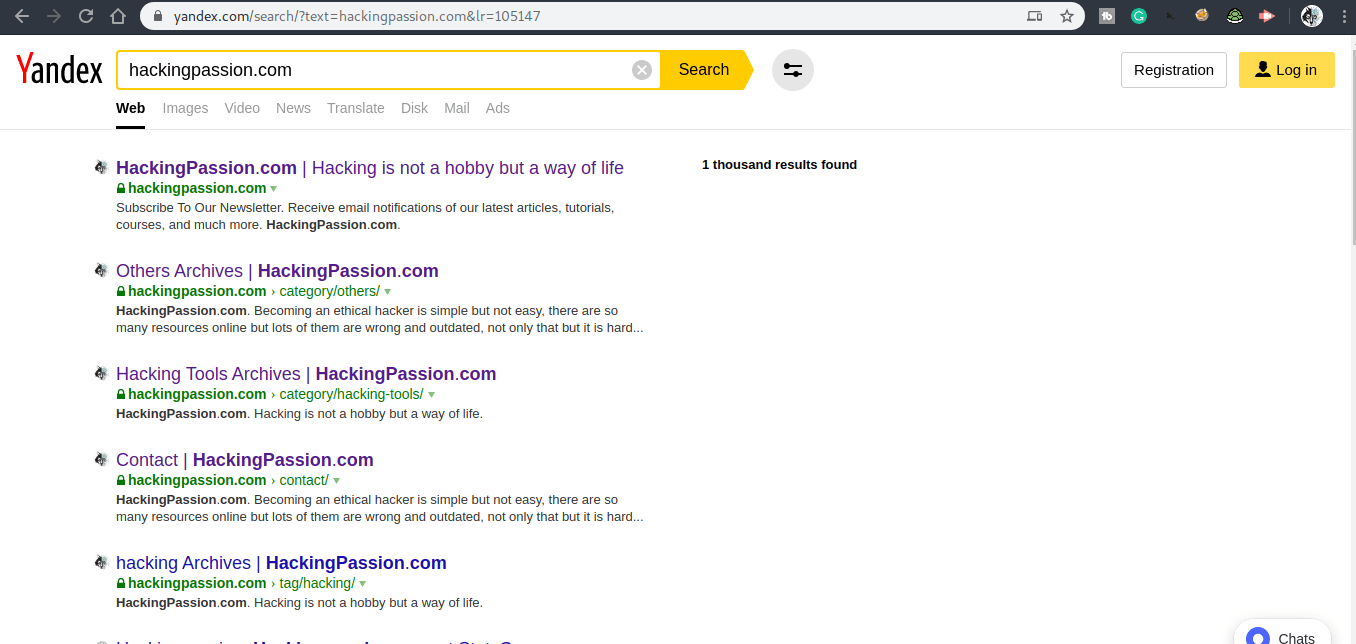
The Dork Finder is a handy tool. In my article “Google Dorks an Easy Way of Hacking” I show what you can do with “Google” Dorks. Really and definitely recommended to read if you are not familiar with Dorks ..!
Also, I made a list of 10.000 Dorks. You can find that on my GitHub page. “Google helps you to find Vulnerable Websites that Indexed in Google Search Results. Here is the latest collection of Google Dorks. A collection of around 10.000 Dorks ..! This list is regularly updated !..”
Google Dork List
https://github.com/BullsEye0/google_dork_list
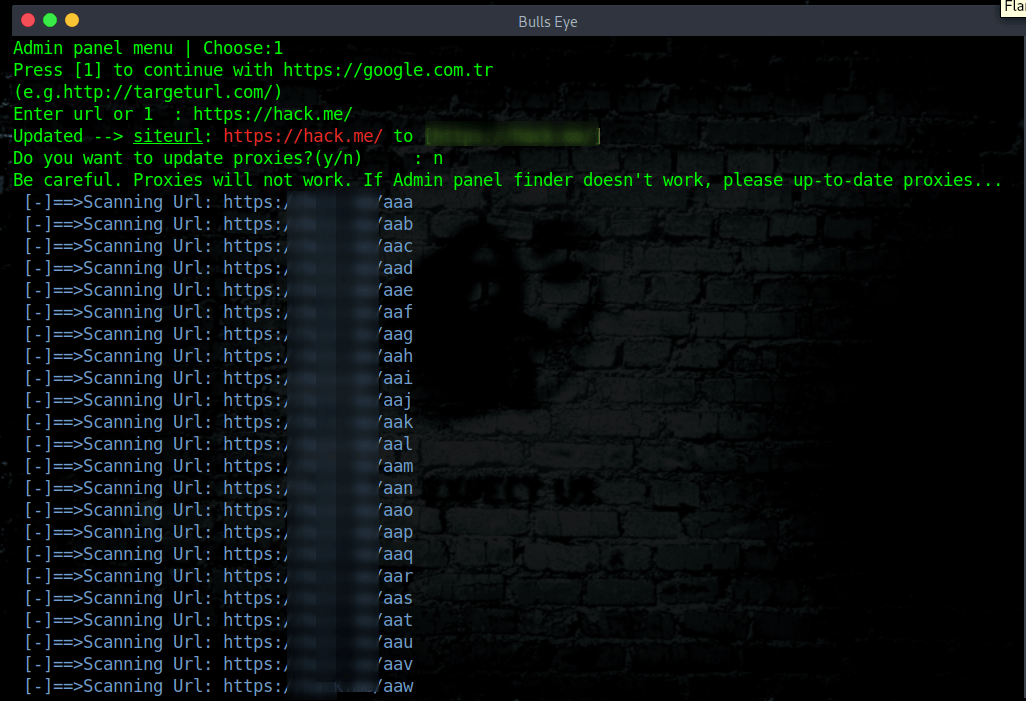
Admin Panel Finder
https://github.com/capture0x/XCTR-Hacking-Tools#admin-panel-finder
In this section, firstly need to choose a wordlist for scanning. Press 2 to change the wordlist and log in.
Url should be https://targetsite.com/ (http or s and / symbol at the end of the url.)
If scanning is slow you will update the proxies. (Press 3 to update)
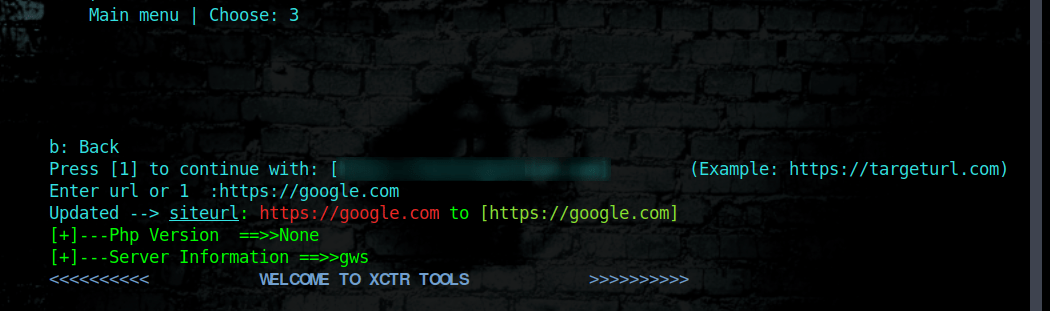
Cms Finder XCTR Hacking Tools
https://github.com/capture0x/XCTR-Hacking-Tools#cms-finder
You’ll find cms version from meta name.
Ip History
https://github.com/capture0x/XCTR-Hacking-Tools#ip-history
This tool displays and save the ip history of the domain.
e.g usage:
| |
Reverse Ip
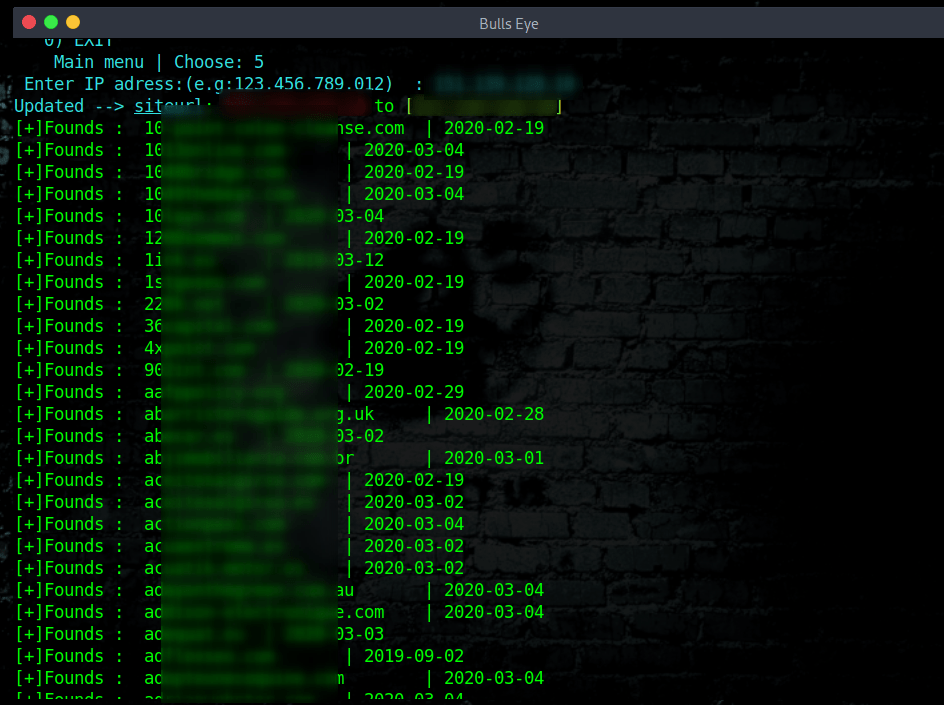
https://github.com/capture0x/XCTR-Hacking-Tools#reverse-ip
With this tool, you can find domains on server.
e.g usage:
| |
Page Viewer
https://github.com/capture0x/XCTR-Hacking-Tools#page-viewer
You can increase the number of page views of the target site.
e.g usage:
| |
XCTR Proxy Finder
https://github.com/capture0x/XCTR-Hacking-Tools#proxy-finder
This tool finds proxies on free-proxy-list.net and updates proxy.txt on the main directory.
Settings
Number 9 gives you the option to adjust the settings of the tool and projects.
Video XCTR Hacking Tools
In this video ill show, you how to install and use the XCTR Hacking Tools.
Become a member on Odysee.com
Earning on Odysee for watching videos ♥️
Here an invitation link, so that we both benefit.
In this way, you also support my work.
https://odysee.com/$/invite/@hackingpassion:9
Conclusion XCTR Hacking Tools
As I mentioned above, I think it’s a great tool and can be a good addition to your Tools lists. It is important that if you use the Admin Panel Finder you do not forget to put the “/” after the URL. Otherwise, it won’t work. I personally think the Dork Finder is especially great.
WANT TO SUPPORT THE WEBSITE
Dear people, I do a lot of things on the Internet and I do it all for free. If I don’t get enough to support myself, it becomes very difficult to maintain my web presence, which takes a lot of time, and the server costs also have to be paid. Your support is greatly appreciated.
Thanks guys ..!
https://paypal.me/hackingpassion
Use the link above to donate via PayPal.
IMPORTANT THINGS TO REMEMBER
✓ This Video and Article is made for educational purposes and pentest only.
✓ You will not misuse the information to gain unauthorized access.
✓ This information shall only be used to expand knowledge and not for causing malicious or damaging attacks…!
Read also the Disclaimer
All the techniques provided in the tutorials on HackingPassion.com, are meant for educational purposes only.
If you are using any of those techniques for illegal purposes, HackingPassion.com can’t be held responsible for possible lawful consequences.
My goal is to educate people and increase awareness by exposing methods used by real black-hat hackers and show how to secure systems from these hackers.
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.